kubernetes,service详解下
HeadLiness类型的Service
在某些场景中,开发人员可能不想使用Service提供的负载均衡功能,而希望自己来控制负载均衡策略,针对这种情况,kubernetes提供了HeadLiness Service,这类Service不会分配Cluster IP,如果想要访问service,只能通过service的域名进行查询。
创建service-headliness.yaml
apiVersion: v1
kind: Service
metadata:name: service-headlinessnamespace: lh
spec:selector:app: nginx-podclusterIP: None type: ClusterIPports:- port: 80 targetPort: 80创建service,获取service, 发现CLUSTER-IP未分配
[root@master ~]# kubectl create -f service-headliness.yaml
service/service-headliness created
[root@master ~]# kubectl get svc service-headliness -n lh -o wide
NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE SELECTOR
service-headliness ClusterIP None <none> 80/TCP 26s app=nginx-pod查看service详情
[root@master ~]# kubectl describe svc service-headliness -n lh
Name: service-headliness
Namespace: lh
Labels: <none>
Annotations: <none>
Selector: app=nginx-pod
Type: ClusterIP
IP Family Policy: SingleStack
IP Families: IPv4
IP: None
IPs: None
Port: <unset> 80/TCP
TargetPort: 80/TCP
Endpoints: <none>
Session Affinity: None
Events: <none>查看域名的解析情况
[root@master ~]# kubectl exec -it pc-deployment-66cb59b984-8p84h -n lh /bin/sh
/ # cat /etc/resolv.conf
nameserver 10.96.0.10
search dev.svc.cluster.local svc.cluster.local cluster.local[root@master ~]# dig @10.96.0.10 service-headliness.dev.svc.cluster.local
service-headliness.dev.svc.cluster.local. 30 IN A 10.244.1.40
service-headliness.dev.svc.cluster.local. 30 IN A 10.244.1.39
service-headliness.dev.svc.cluster.local. 30 IN A 10.244.2.33
//想要访问的话,需要在pod里面的容器进行访问,需要先运行一个pod起来,然后进入容器,进行访问
kubectl run busybox11 --image busybox -n dev -- sleep 6000
kubectl exec -itn dev -n dev busybox11 -- /bin/sh
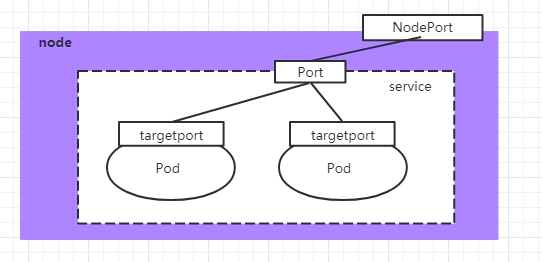
//进入容器后,使用wget -O - -q service-headliness就可以访问了NodePort类型的Service
在之前的样例中,创建的Service的ip地址只有集群内部才可以访问,如果希望将Service暴露给集群外部使用,那么就要使用到另外一种类型的Service,称为NodePort类型。NodePort的工作原理其实就是将service的端口映射到Node的一个端口上,然后就可以通过NodeIp:NodePort来访问service了。
创建service-nodeport.yaml
apiVersion: v1
kind: Service
metadata:name: service-nodeportnamespace: lh
spec:selector:app: nginx-podtype: NodePort ports:- port: 80nodePort: 30002targetPort: 80创建service,并查看service
[root@master ~]# kubectl get svc -n lh -o wide
NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE SELECTOR
service-headliness ClusterIP None <none> 80/TCP 18m app=nginx-pod
service-nodeport NodePort 10.110.136.75 <none> 80:30002/TCP 9s app=nginx-pod接下来可以通过电脑主机的浏览器去访问集群中任意一个nodeip的30002端口,即可访问到pod
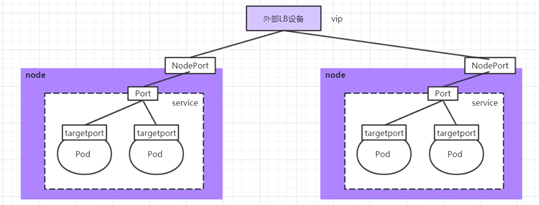
LoadBalancer类型的Service
LoadBalancer和NodePort很相似,目的都是向外部暴露一个端口,区别在于LoadBalancer会在集群的外部再来做一个负载均衡设备,而这个设备需要外部环境支持的,外部服务发送到这个设备上的请求,会被设备负载之后转发到集群中。
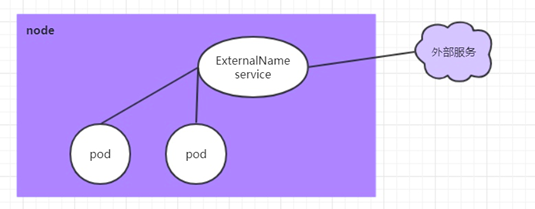
ExternalName类型的Service
ExternalName类型的Service用于引入集群外部的服务,它通过externalName属性指定外部一个服务的地址,然后在集群内部访问此service就可以访问到外部的服务了。
创建service-externalname.yaml文件
apiVersion: v1
kind: Service
metadata:name: service-externalnamenamespace: lh
spec:type: ExternalName externalName: www.baidu.com 创建service,域名解析
[root@master ~]# kubectl create -f service-externalname.yaml
service/service-externalname created
[root@master ~]# dig @10.96.0.10 service-externalname.dev.svc.cluster.local
service-externalname.dev.svc.cluster.local. 30 IN CNAME www.baidu.com.
www.baidu.com. 30 IN CNAME www.a.shifen.com.
www.a.shifen.com. 30 IN A 39.156.66.18
www.a.shifen.com. 30 IN A 39.156.66.14Ingress介绍
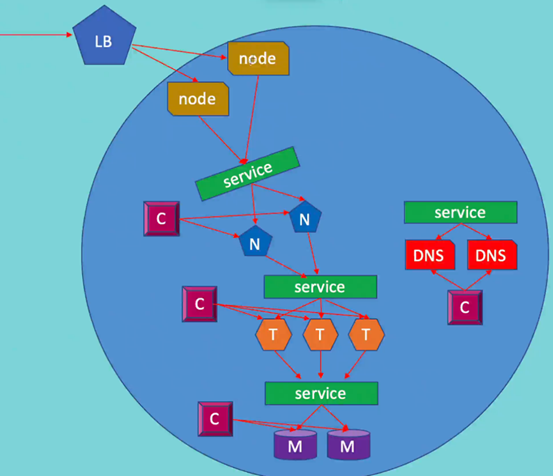
在上面已经提到,Service对集群之外暴露服务的主要方式有两种:NotePort和LoadBalancer,但是这两种方式,都有一定的缺点:
• NodePort方式的缺点是会占用很多集群机器的端口,那么当集群服务变多的时候,这个缺点就愈发明显
• LB方式的缺点是每个service需要一个LB,浪费、麻烦,并且需要kubernetes之外设备的支持
基于这种现状,kubernetes提供了Ingress资源对象,Ingress只需要一个NodePort或者一个LB就可以满足暴露多个Service的需求。工作机制大致如下图表示:
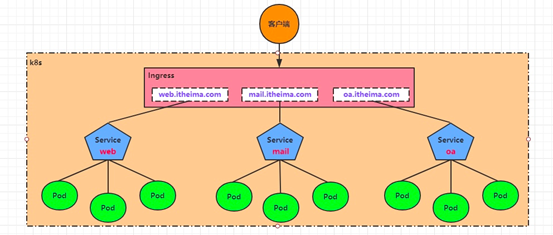
实际上,Ingress相当于一个7层的负载均衡器,是kubernetes对反向代理的一个抽象,它的工作原理类似于Nginx,可以理解成在Ingress里建立诸多映射规则,Ingress Controller通过监听这些配置规则并转化成Nginx的反向代理配置 , 然后对外部提供服务。在这里有两个核心概念:
• ingress:kubernetes中的一个对象,作用是定义请求如何转发到service的规则
• ingress controller:具体实现反向代理及负载均衡的程序,对ingress定义的规则进行解析,根据配置的规则来实现请求转发,实现方式有很多,比如Nginx, Contour, Haproxy等等
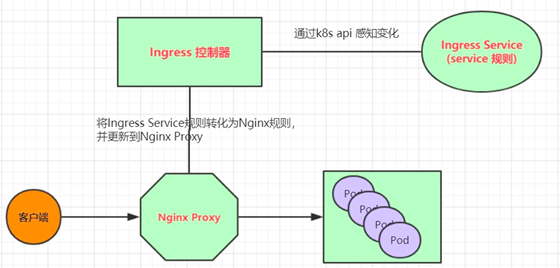
Ingress(以Nginx为例)的工作原理如下:
- 用户编写Ingress规则,说明哪个域名对应kubernetes集群中的哪个Service
- Ingress控制器动态感知Ingress服务规则的变化,然后生成一段对应的Nginx反向代理配置
- Ingress控制器会将生成的Nginx配置写入到一个运行着的Nginx服务中,并动态更新
- 到此为止,其实真正在工作的就是一个Nginx了,内部配置了用户定义的请求转发规则
Ingress使用
环境准备
搭建ingress环境
创建文件夹
[root@master ~]# mkdir ingress-controller
[root@master ~]# cd ingress-controller/在github官网上查找ingress对应的yaml文件并下载下来
https://raw.githubusercontent.com/kubernetes/ingress-nginx/main/deploy/static/provider/baremetal/deploy.yaml
[root@master ingress-controller]# wget https://raw.githubusercontent.com/kubernetes/ingress-nginx/main/deploy/static/provider/baremetal/deploy.yaml修改yaml内容
- name: LD_PRELOADvalue: /usr/local/lib/libmimalloc.soimage: dyrnq/ingress-nginx-controller:v1.5.1imagePullPolicy: IfNotPresentlifecycle:- name: POD_NAMESPACEvalueFrom:fieldRef:fieldPath: metadata.namespaceimage: lianyuxue1020/kube-webhook-certgen:v1.1.1imagePullPolicy: IfNotPresentname: createsecurityContext:allowPrivilegeEscalation: false- name: POD_NAMESPACEvalueFrom:fieldRef:fieldPath: metadata.namespaceimage: lianyuxue1020/kube-webhook-certgen:v1.1.1imagePullPolicy: IfNotPresent应用
[root@master ingress-controller]# kubectl apply -f deploy.yaml
namespace/ingress-nginx created
serviceaccount/ingress-nginx created
serviceaccount/ingress-nginx-admission created
role.rbac.authorization.k8s.io/ingress-nginx created
role.rbac.authorization.k8s.io/ingress-nginx-admission created
clusterrole.rbac.authorization.k8s.io/ingress-nginx created
clusterrole.rbac.authorization.k8s.io/ingress-nginx-admission created
rolebinding.rbac.authorization.k8s.io/ingress-nginx created
rolebinding.rbac.authorization.k8s.io/ingress-nginx-admission created
clusterrolebinding.rbac.authorization.k8s.io/ingress-nginx created
clusterrolebinding.rbac.authorization.k8s.io/ingress-nginx-admission created
configmap/ingress-nginx-controller created
service/ingress-nginx-controller created
service/ingress-nginx-controller-admission created
deployment.apps/ingress-nginx-controller created
job.batch/ingress-nginx-admission-create created
job.batch/ingress-nginx-admission-patch created
ingressclass.networking.k8s.io/nginx created
validatingwebhookconfiguration.admissionregistration.k8s.io/ingress-nginx-admission created查看
[root@master ingress-controller]# kubectl get svc -n ingress-nginx
NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE
ingress-nginx-controller NodePort 10.104.199.252 <none> 80:31281/TCP,443:31750/TCP 73s
ingress-nginx-controller-admission ClusterIP 10.108.255.10 <none> 443/TCP 73s[root@master ingress-controller]# kubectl get pod -n ingress-nginx
NAME READY STATUS RESTARTS AGE
ingress-nginx-admission-create-2nfhc 0/1 Completed 0 89s
ingress-nginx-admission-patch-r9l6r 0/1 Completed 1 89s
ingress-nginx-controller-6f66fd4bdb-mjf6g 1/1 Running 0 89s准备service和pod
为了后面的实验比较方便,创建如下图所示的模型
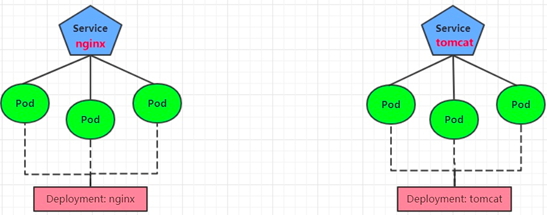
创建tomcat-nginx.yaml
apiVersion: apps/v1
kind: Deployment
metadata:name: nginx-deploymentnamespace: lh
spec:replicas: 3selector:matchLabels:app: nginx-podtemplate:metadata:labels:app: nginx-podspec:containers:- name: nginximage: nginx:1.17.1ports:- containerPort: 80
---apiVersion: apps/v1
kind: Deployment
metadata:name: tomcat-deploymentnamespace: lh
spec:replicas: 3selector:matchLabels:app: tomcat-podtemplate:metadata:labels:app: tomcat-podspec:containers:- name: tomcatimage: tomcat:8.5-jre10-slimports:- containerPort: 8080
---apiVersion: v1
kind: Service
metadata:name: nginx-servicenamespace: lh
spec:selector:app: nginx-podclusterIP: Nonetype: ClusterIPports:- port: 80targetPort: 80
---apiVersion: v1
kind: Service
metadata:name: tomcat-servicenamespace: lh
spec:selector:app: tomcat-podclusterIP: Nonetype: ClusterIPports:- port: 8080targetPort: 8080创建并查看
[root@master ingress-controller]# kubectl create -f tomcat-nginx.yaml
deployment.apps/nginx-deployment created
deployment.apps/tomcat-deployment created
service/nginx-service created
service/tomcat-service created
[root@master ingress-controller]# kubectl get svc -n lh
NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE
nginx-service ClusterIP None <none> 80/TCP 10stomcat-service ClusterIP None <none> 8080/TCP 10sHttp代理
创建ingress-http.yaml
apiVersion: networking.k8s.io/v1
kind: Ingress
metadata:name: ingress-httpnamespace: lh
spec:ingressClassName: nginxrules:- host: nginx.xuanning.comhttp:paths:- path: /pathType: Prefixbackend:service:name: nginx-serviceport: number: 80- host: tomcat.xuanning.comhttp:paths:- path: /pathType: Prefixbackend:service:name: tomcat-serviceport: number: 8080创建并查看
[root@master ingress-controller]# kubectl create -f ingress-http.yaml
ingress.networking.k8s.io/ingress-http created
[root@master ingress-controller]# kubectl get -f ingress-http.yaml
NAME CLASS HOSTS ADDRESS PORTS AGE
ingress-http nginx nginx.xuanning.com,tomcat.xuanning.com 80 12s
[root@master ingress-controller]# kubectl describe ingress ingress-http -n lh
Name: ingress-http
Labels: <none>
Namespace: lh
Address:
Ingress Class: nginx
Default backend: <default>
Rules:Host Path Backends---- ---- --------nginx.xuanning.com/ nginx-service:80 (10.244.1.7:80,10.244.2.61:80,10.244.2.62:80)tomcat.xuanning.com/ tomcat-service:8080 (10.244.1.8:8080,10.244.1.9:8080,10.244.2.63:8080)需要查看只需修改本地的host文件即可
Https代理
注意http和https只能定义一个,先删除http的
创建证书
生成证书
[root@master ingress-controller]# openssl req -x509 -sha256 -nodes -days 365 -newkey rsa:2048 -keyout tls.key -out tls.crt -subj "/C=CN/ST=BJ/L=BJ/O=nginx/CN=xuanning.com"创建密钥
[root@master ingress-controller]# kubectl create secret tls tls-secret --key tls.key --cert tls.crt
secret/tls-secret created创建ingress-https.yaml
apiVersion: networking.k8s.io/v1
kind: Ingress
metadata:name: ingress-httpsnamespace: lh
spec:tls:- hosts:- nginx.xuanning.com- tomcat.xuanning.comsecretName: tls-secretingressClassName: nginxrules: - host: nginx.xuanning.comhttp:paths:- path: /pathType: Prefixbackend:service: name: nginx-serviceport: number: 80- host: tomcat.xuanning.comhttp:paths:- path: /pathType: Prefixbackend:service: name: tomcat-serviceport: number: 8080创建并查看
[root@master ingress-controller]# kubectl create -f ingress-https.yaml
ingress.networking.k8s.io/ingress-https created
[root@master ingress-controller]# kubectl get ing ingress-https -n lh
NAME CLASS HOSTS ADDRESS PORTS AGE
ingress-https nginx nginx.xuanning.com,tomcat.xuanning.com 80, 443 9s
[root@master ingress-controller]# kubectl describe ing ingress-https -n lh
Name: ingress-https
Labels: <none>
Namespace: lh
Address:
Ingress Class: nginx
Default backend: <default>
TLS:tls-secret terminates nginx.xuanning.com,tomcat.xuanning.com
Rules:Host Path Backends---- ---- --------nginx.xuanning.com/ nginx-service:80 (10.244.1.7:80,10.244.2.61:80,10.244.2.62:80)tomcat.xuanning.com/ tomcat-service:8080 (10.244.1.8:8080,10.244.1.9:8080,10.244.2.63:8080)如需访问只要修改本地host文件即可
![[附源码]Python计算机毕业设计SSM健身房管理系统 (程序+LW)](https://img-blog.csdnimg.cn/4db19bd817d44493bdfe5075a4304682.png)