请访问原文链接:sysin.org/blog/junipe…,查看最新版。原创作品,转载请保留出处。
作者:gc(at)sysin.org,主页:www.sysin.org
防火墙 HA 配置系列文章:
- Cisco Firepower FTD HA 配置文档
- FortiGate FGCP HA 配置文档
- Palo Alto PAN-OS Active/Passive HA 配置文档
- Juniper SRX JSRP 配置文档
SRX 机箱群集(Chassis Cluster)又称为 Junos 服务冗余协议(JSRP),它通过将一对相同类型的支持瞻博网络安全路由器或 SRX 系列服务网关组合到一个群集中来提供网络节点冗余。设备必须使用增强的服务运行 Junos OS。
这两个节点通过一个节点作为主设备,另一个是备份设备,在发生系统或硬件故障时确保进程和服务的状态故障转移。如果主节点发生故障,辅助节点将接管信息流处理。群集中的节点通过以太网链路互连,并在整个群集中同步配置、内核和会话状态,从而促进接口和服务的高可用性。
机箱群集功能包括:
- 弹性系统架构,具有整个群集的单一活动控制平面和多个数据包转发引擎,提供了群集的单一服务网关视图。
- 群集中节点之间的配置和动态运行时状态同步。
- 如果故障参数交叉于配置的阈值,则监控物理接口和故障转移。
一、准备篇
1. 设备登录
console 口登录,初始默认用户名 root,密码为空
root% cli /*** 进入操作模式 ***/
root>
root> configure
Entering configuration mode /*** 进入配置模式 ***/
[edit]
Root#
2. 恢复出厂设置
root# load factory-default
同时设置密码:
root# set system root-authentication plain-text-password
提示输入并确认密码,然后确认并重启
设置远程登录管理用户:
root# set system login user admin class super-user authentication plain-text-password
root# new password :
root# retype new password:
// 添加另外一个用户:
set system login user sysin class super-user authentication plain-text-password
补充:通过 RESET CONFIG 按键恢复出厂设置
To reset the device to its factory default configuration, press and hold the Reset Config button on the front panel of the SRX Series device for at least 15 seconds, until the Status LED glows amber.
注意:所有配置和备份都降丢失,按下 RESET CONFIG 按钮,保持 15 秒以上,直到 Status LED 灯变成琥珀色
3. 网线连接
(1)HA 带外管理端口 MGMT,即 fxp0,线缆接入交换机
- For SRX100 devices, connect the fe-0/0/6 port to the fe-1/0/6 port
- For SRX210 devices, connect the fe-0/0/6 port to the fe-2/0/6 port
- For SRX240 devices, connect the ge-0/0/0 port to the ge-5/0/0 port
- For SRX550 devices, connect the ge-0/0/0 port to the ge-9/0/0 port
- For SRX650 devices, connect the ge-0/0/0 port to the ge-9/0/0 port
2019 年更新
- SRX300, ge-0/0/0 <—> ge-1/0/0
- SRX320, ge-0/0/0 <—> ge-3/0/0
- SRX340/345, 专有管理口
- SRX550, ge-0/0/0 <—> ge-9/0/0
- SRX1500, 专有管理口
SRX high-end 系列有专有管理端口
(2)HA 控制信号端口 Control Port,即 fxp1,线缆直连
你必须使用下面设备指定端口来作为 HA 控制信号端口进行互连,即 fxp1
- For SRX100 devices, connect the fe-0/0/7 port to the fe-1/0/7 port
- For SRX210 devices, connect the fe-0/0/7 port to the fe-2/0/7 port
- For SRX240 devices, connect the ge-0/0/1 port to the ge-5/0/1 port
- For SRX550 devices, connect the ge-0/0/1 port to the ge-9/0/1 port
- For SRX650 devices, connect the ge-0/0/1 port to the ge-9/0/1 port
2019 年更新
- SRX300, ge-0/0/1 <—> ge-1/0/1
- SRX320, ge-0/0/1 <—> ge-3/0/1
- SRX340/345, ge-0/0/1 <—> ge-5/0/1
- SRX550, ge-0/0/1 <—> ge-9/0/1
- SRX1500, 专有控制口
SRX High-End 系列有专有控制端口
补充说明:
SRX550 标准配置 6 个千兆以太网口,只能部署单线的 HA 结构,双线必须增加接口板卡
SRX650 标准配置 4 个千兆以太网口,如果需要部署 HA 结构,则必须增加数据接口板卡 <因为 HA 控制平面、数据平面和带外管理接口被占用了至少 3 个接口>
(3)HA 数据接口即 Fabric Port,可以指定任意物理接口(SRX High-End 相同),线缆直连
node0 中为 fab0,node1 中为 fab1
备注:SRX4000 系列(4100、4200、4600)有专有 Fab 端口
2019 年更新新产品:参看官网文档
网线连接实例:
- SRX240 连接网线(SRX550 和 SRX650 相同)* 0/0 带外管理 MGMT* 0/1 直连,Control* 0/2 直连,Fabric(可指定其他任意端口)
- SRX340/345 连接网线* MGMT 带外管理 专有口* 0/1 直连,Control* 0/2 直连,Fabric(可指定其他人任意端口)
- SRX1500 连接网线* MGMT 带外管理,专有口 MGMT* HA CONTROL 直连,专有口 Control* 0/0 直连,Fabric(可指定其他人任意端口)
4. 在低端设备上禁用交换
来自官方文档(原文链接失效):Disabling Switching on SRX100, SRX210, SRX220, and SRX240 Devices Before Enabling Chassis Clustering
实际要删除更多的配置。
delete system autoinstallation
delete system services dhcp
delete system services web-management http interface vlan.0
delete system services web-management https interface vlan.0
delete interfaces interface-range interfaces-trust
delete interfaces vlan
delete security zones security-zone trust
delete security nat
delete security zones security-zone untrust
delete security policies
delete vlansdelete interfaces ge-0/0/0
delete interfaces ge-0/0/1
delete interfaces ge-0/0/2
delete interfaces ge-0/0/3
delete interfaces ge-0/0/4
delete interfaces ge-0/0/5
delete interfaces ge-0/0/6
delete interfaces ge-0/0/7
delete interfaces ge-0/0/8
delete interfaces ge-0/0/9
delete interfaces ge-0/0/10
delete interfaces ge-0/0/11
delete interfaces ge-0/0/12
delete interfaces ge-0/0/13
delete interfaces ge-0/0/14
delete interfaces ge-0/0/15
下图是一个最简单的拓扑参考:
二、配置篇
整个 JSRP 配置过程包括如下 7 个步骤。
- 配置 Cluster id 和 Node id (对应 ScreenOS NSRP 的 cluster id 并需手工指定设备使用节点 id)
- 指定 Control Port (指定控制层面使用接口,用于配置同步及心跳)
- 指定 Fabric Link Port (指定数据层面使用接口,主要 session 等 RTO 同步)
- 配置 Redundancy Group (类似 NSRP 的 VSD group,优先级与抢占等配置)
- 每个机箱的个性化配置 (单机无需同步的个性化配置,如主机名、带外管理口 IP 地址等)
- 配置 Redundant Ethernet Interface (类似 NSRP 的 Redundant 冗余接口)
- 配置 Interface Monitoring (类似 NSRP interface monitor,是 RG 数据层面切换依据)
以下 SRX JSRP 配置样例,基于 SRX240 和 SRX3400:
分别修改两台 SRX 主机名如下:
root@SRX#set system host-name SRX-A
root@SRX#set system host-name SRX-B
1. 配置 Cluster id 和 Node id
SRX-A>set chassis cluster cluster-id 1 node 0 reboot
// 注意该命令需在 operational 模式下输入
Cluster ID 取值范围为 1 – 15,当 Cluster ID = 0 时将 unsets the cluster),node-id 取值 0 - 1
SRX-B>set chassis cluster cluster-id 1 node 1 reboot
注意:虚 IP 的 MAC 地址,是由 cluter-id 决定的,在同一网段的两组设备可能冲突,注意配置不同的 cluter-id 经过测试,配置后可以更改 cluter-id,分别在两个 node 上执行上述命令即可 Redundant Ethernet interface 的 MAC 地址是虚拟的,其值根据以下公式可以计算得出: 0010DB11111111CCCCRRVV1111111 CCCC: Cluster ID RR: Reserved. 00. VV: Version, 00 for the first release IIIIIIII: Interface id, derived from the reth index.
2. 指定 Control Port
- SRX Branch 系列,则无需指定,默认规定采用某一个接口作为控制接口,参考上一节
- SRX hign-end 系列有专用 Control 端口
3. 指定 Fabric Link Port
set interfaces fab0 fabric-options member-interfaces ge-0/0/2
set interfaces fab1 fabric-options member-interfaces ge-5/0/2
注:Fabric Link 中的 Fab0 固定用于 node 0,Fab1 固定用于 node 1
4. 配置 Redundancy Group
RG0 固定用于主控板 RE 切换,RG1 以后用于 redundant interface 切换,RE 切换独立于接口切换
set chassis cluster reth-count 10//(指定整个 Cluster 中 redundant ethernet interface 最多数量)
set chassis cluster redundancy-group 0 node 0 priority 200//(取值范围 1-254,高值优先,与 NSRP 相反)
set chassis cluster redundancy-group 0 node 1 priority 100
set chassis cluster redundancy-group 1 node 0 priority 200//(取值范围 1-254,高值优先,与 NSRP 相反)
set chassis cluster redundancy-group 1 node 1 priority 100
5. 每个机箱的个性化配置,便于对两台设备的区分与管理
set groups node0 system host-name SRX-A
set groups node0 interfaces fxp0 unit 0 family inet address 10.3.2.251/24//(带外网管口名称为 fxp0,区别 ScreenOS 的 MGT 口)
set groups node1 system host-name SRX-B
set groups node1 interfaces fxp0 unit 0 family inet address 10.3.2.252/24set apply-groups ${node} //(应用上述 groups 配置)
配置带外管理口 backup-router
The backup-router destination of 0.0.0.0/0 is not recommended, and should be avoided.
set groups node0 system backup-router 10.3.2.1 destination 10.3.0.0/16
set groups node1 system backup-router 10.3.2.1 destination 10.3.0.0/16
关于带外管理口的 fxp0
不属于任何安全区域
需要 ssh 服务开启(set system services ssh)才能访问
需要配置 backup-router 以便非相同子网的远程管理客户端访问
6. 配置 Redundant Ethernet Interface
Redundant Ethernet Interface 类 似 ScreenOS 里 的 redundant interface,只不过 Redundant Ethernet interface 是分布在不同的机箱上 (这一特性又类似 ScreenOS 的 VSI 接口)。
本例是电信和联通双线网络
// 内网口
set interface ge-0/0/3 gigether-options redundant-parent reth0//(node 0 的 ge-0/0/3 接口)
set interface ge-5/0/3 gigether-options redundant-parent reth0//(node 1 的 ge-0/0/3 接口)
set interface reth0 redundant-ether-options redundancy-group 1//(reth0 属于 RG1)
set interface reth0 unit 0 family inet address 10.3.1.254/24
// 电信外部
set interface ge-0/0/4 gigether-options redundant-parent reth1
set interface ge-5/0/4 gigether-options redundant-parent reth1
set interface reth1 redundant-ether-options redundancy-group 1
set interface reth1 unit 0 family inet address 122.226.95.226/28
// 电信内部
set interface ge-0/0/5 gigether-options redundant-parent reth2
set interface ge-5/0/5 gigether-options redundant-parent reth2
set interface reth2 redundant-ether-options redundancy-group 1
set interface reth2 unit 0 family inet address 122.226.95.254/28
// 联通外部
set interface ge-0/0/6 gigether-options redundant-parent reth3
set interface ge-5/0/6 gigether-options redundant-parent reth3
set interface reth3 redundant-ether-options redundancy-group 1
set interface reth3 unit 0 family inet address 192.168.1.1/24
// 联通内部
set interface ge-0/0/7 gigether-options redundant-parent reth4
set interface ge-5/0/7 gigether-options redundant-parent reth4
set interface reth4 redundant-ether-options redundancy-group 1
set interface reth4 unit 0 family inet address 192.168.100.1/24
7. 配置 Interface Monitoring
被监控的接口 Down 掉后,RG1 将自动进行主备切换(与 ScreenOS 类似)
set chassis cluster redundancy-group 1 interface-monitor ge-0/0/3 weight 255
set chassis cluster redundancy-group 1 interface-monitor ge-0/0/4 weight 255
set chassis cluster redundancy-group 1 interface-monitor ge-0/0/5 weight 255
set chassis cluster redundancy-group 1 interface-monitor ge-0/0/6 weight 255
set chassis cluster redundancy-group 1 interface-monitor ge-0/0/7 weight 255set chassis cluster redundancy-group 1 interface-monitor ge-5/0/3 weight 255
set chassis cluster redundancy-group 1 interface-monitor ge-5/0/4 weight 255
set chassis cluster redundancy-group 1 interface-monitor ge-5/0/5 weight 255
set chassis cluster redundancy-group 1 interface-monitor ge-5/0/6 weight 255
set chassis cluster redundancy-group 1 interface-monitor ge-5/0/7 weight 255
以上群集配置完成,以下开始网络和策略配置
8. 配置安全区域
set security zones security-zone trust interfaces reth0.0
set security zones security-zone trust host-inbound-traffic system-services all
set security zones security-zone trust host-inbound-traffic protocols allset security zones security-zone CT-sysin-Outside interfaces reth1.0
//set security zones security-zone CT-sysin-Outside host-inbound-traffic system-services all// 配置 ssh,ping 即可
set security zones security-zone CT-sysin-Outside host-inbound-traffic system-services ssh
set security zones security-zone CT-sysin-Outside host-inbound-traffic system-services ping
set security zones security-zone CT-sysin-Outside host-inbound-traffic protocols allset security zones security-zone CT-sysin-Inside interfaces reth2.0
set security zones security-zone CT-sysin-Inside host-inbound-traffic system-services all
set security zones security-zone CT-sysin-Inside host-inbound-traffic protocols allset security zones security-zone CU-sysin-Outside interfaces reth3.0
//set security zones security-zone CU-sysin-Outside host-inbound-traffic system-services all// 配置 ssh,ping 即可
set security zones security-zone CU-sysin-Outside host-inbound-traffic system-services ssh
set security zones security-zone CU-sysin-Outside host-inbound-traffic system-services ping
set security zones security-zone CU-sysin-Outside host-inbound-traffic protocols allset security zones security-zone CU-sysin-Inside interfaces reth4.0
set security zones security-zone CU-sysin-Inside host-inbound-traffic system-services all
set security zones security-zone CU-sysin-Inside host-inbound-traffic protocols all
9. 配置路由
set routing-options interface-routes rib-group inet inside
set routing-options static route 0.0.0.0/0 next-hop 122.226.95.225// 默认网关指向电信或者联通默认网关,看来只能默认从一条线路出?
set routing-options static route 10.3.0.0/16 next-hop 10.3.1.10// 内部网络指向核心交换
set routing-options rib-groups inside import-rib inet.0set routing-options rib-groups inside import-rib CT.inet.0
set routing-options rib-groups inside import-rib CU.inet.0set routing-instances CT instance-type virtual-router
set routing-instances CT interface reth1.0
set routing-instances CT interface reth2.0
set routing-instances CT routing-options interface-routes rib-group inet inside// 这句可以不用配置,配置后实例路由表包含其他实例的条目
set routing-instances CT routing-options static route 122.226.95.240/28 next-hop 122.226.95.253// 电信内部 IP 段指向 F5,可以不用配置
set routing-instances CT routing-options static route 0.0.0.0/0 next-hop 122.226.95.225 // 电信外部 IP 段默认网关set routing-instances CU instance-type virtual-router
set routing-instances CU interface reth3.0
set routing-instances CU interface reth4.0
set routing-instances CU routing-options interface-routes rib-group inet inside// 这句可以不用配置,配置后实例路由表包含其他实例的标目
set routing-instances CU routing-options static route 192.168.100.64/24 next-hop 192.168.100.4// 联通外部 IP 段指向 F5,可以不用配置
set routing-instances CU routing-options static route 0.0.0.0/0 next-hop 192.168.1.1// 联通外部 IP 段默认网关
10. 设置安全策略
// 电信内部到电信外部,默认允许
set security policies from-zone CT-sysin-Inside to-zone CT-sysin-Outside policy CT-Outbound match source-address any
set security policies from-zone CT-sysin-Inside to-zone CT-sysin-Outside policy CT-Outbound match destination-address any
set security policies from-zone CT-sysin-Inside to-zone CT-sysin-Outside policy CT-Outbound match application any
set security policies from-zone CT-sysin-Inside to-zone CT-sysin-Outside policy CT-Outbound then permit// 电信外部到电信内部,允许特定协议
set security policies from-zone CT-sysin-Outside to-zone CT-sysin-Inside policy CT-Inbound match source-address any
set security policies from-zone CT-sysin-Outside to-zone CT-sysin-Inside policy CT-Inbound match destination-address any
set security policies from-zone CT-sysin-Outside to-zone CT-sysin-Inside policy CT-Inbound match application junos-http
set security policies from-zone CT-sysin-Outside to-zone CT-sysin-Inside policy CT-Inbound match application junos-https
set security policies from-zone CT-sysin-Outside to-zone CT-sysin-Inside policy CT-Inbound match application junos-icmp-all
set security policies from-zone CT-sysin-Outside to-zone CT-sysin-Inside policy CT-Inbound match application junos-smtp
set security policies from-zone CT-sysin-Outside to-zone CT-sysin-Inside policy CT-Inbound match application TCP-8080
set security policies from-zone CT-sysin-Outside to-zone CT-sysin-Inside policy CT-Inbound then permit
set security policies from-zone CT-sysin-Outside to-zone CT-sysin-Inside policy CT-Inbound then log session-close// 联通内部到联通外部,默认允许 // 注意 CU 和 CT 差别
set security policies from-zone CU-sysin-Inside to-zone CU-sysin-Outside policy CU-Outbound match source-address any
set security policies from-zone CU-sysin-Inside to-zone CU-sysin-Outside policy CU-Outbound match destination-address any
set security policies from-zone CU-sysin-Inside to-zone CU-sysin-Outside policy CU-Outbound match application any
set security policies from-zone CU-sysin-Inside to-zone CU-sysin-Outside policy CU-Outbound then permit// 联通外部到联通内部,允许特定协议 // 注意 CU 和 CT 差别
set security policies from-zone CU-sysin-Outside to-zone CU-sysin-Inside policy CU-Inbound match source-address any
set security policies from-zone CU-sysin-Outside to-zone CU-sysin-Inside policy CU-Inbound match destination-address any
set security policies from-zone CU-sysin-Outside to-zone CU-sysin-Inside policy CU-Inbound match application junos-http
set security policies from-zone CU-sysin-Outside to-zone CU-sysin-Inside policy CU-Inbound match application junos-https
set security policies from-zone CU-sysin-Outside to-zone CU-sysin-Inside policy CU-Inbound match application junos-icmp-all
set security policies from-zone CU-sysin-Outside to-zone CU-sysin-Inside policy CU-Inbound match application junos-smtp
set security policies from-zone CU-sysin-Outside to-zone CU-sysin-Inside policy CU-Inbound match application TCP-8080
set security policies from-zone CU-sysin-Outside to-zone CU-sysin-Inside policy CU-Inbound then permit
set security policies from-zone CU-sysin-Outside to-zone CU-sysin-Inside policy CU-Inbound then log session-close// 内部到外部,默认用电信允许全部
set security policies from-zone trust to-zone CT-sysin-Outside policy trust-outbound match source-address any
set security policies from-zone trust to-zone CT-sysin-Outside policy trust-outbound match destination-address any
set security policies from-zone trust to-zone CT-sysin-Outside policy trust-outbound match application any
set security policies from-zone trust to-zone CT-sysin-Outside policy trust-outbound then permit// 电信外部到内部,指定应用
set security policies from-zone CT-sysin-Outside to-zone trust policy policy-1 match source-address any
set security policies from-zone CT-sysin-Outside to-zone trust policy policy-1 match destination-address 10.19.177.231/32
set security policies from-zone CT-sysin-Outside to-zone trust policy policy-1 match application any
set security policies from-zone CT-sysin-Outside to-zone trust policy policy-1 then permit
自定义应用和协议
set applications application TCP-8080 protocol tcp
set applications application TCP-8080 source-port 1-65535
set applications application TCP-8080 destination-port 8080
11. 其他常用配置
- 自定义应用和协议
// 定义一个 TCP 8080 端口的应用
set applications application TCP-8080 protocol tcp
set applications application TCP-8080 source-port 1-65535
set applications application TCP-8080 destination-port 8080// 定义一个 UDP 9999 端口的应用
>set applications application UDP-9999 protocol udp
>set applications application UDP-9999 source-port 1-65535
>set applications application UDP-9999 destination-port 9999
- 时区
set system time-zone Asia/Shanghai
- NTP
set system ntp server 10.3.5.11 version 3
set system ntp server 10.3.5.12 version 3
set system ntp server 10.3.5.11 prefer
//version 3 为 Windows NTP,或者直接配置
set system ntp server 10.3.5.11
set system ntp server 10.3.5.12
- 远程管理服务
set system services ssh
set system services telnet// 可以 delete
set system services xnm-clear-text// 建议 delete
set system services web-management http// 建议 delete
set system services web-management https system-generated-certificate// 可以 delete
- 端口告警设置
set chassis alarm ethernet link-down ignore// 设置全部端口不产生告警
// 注意:link-down 可以侦测端口的状态,如果设置了端口 link down 的 alarm 告警,则不用的端口最好 disable,以避免频繁告警
// 补充:
set chassis alarm ethernet link-down red// 设置全部端口产生告警
- SNMP
set snmp location Beijing
set snmp contact "xxx@domain.com"
set snmp community <abc> authorization read-only// 将 <abc> 修改为自定义的字符
set security zones security-zone trust host-inbound-traffic system-services snmp// 注意开启 zone 的 snmp 服务,这里是 trust
- 关闭 ALG
ALG 应用级网关,也叫做应用层网关(Application Layer Gateway)
set security alg [协议名称] disable
set security alg dns disable
set security alg sql disable
- 针对内网口,设置源地址 nat
set security nat source rule-set trust-to-CT from zone trust
set security nat source rule-set trust-to-CT to zone CT-sysin-Outside
set security nat source rule-set trust-to-CT rule 01 match source-address 10.3.0.0/16// 或者直接 0.0.0.0/0
set security nat source rule-set trust-to-CT rule 01 then source-nat interface
- 设置 DNS(系统默认这条是用 OpenDNS)
set system name-server 208.67.222.222
set system name-server 208.67.220.220
-
配置 syslog* Branch 设备:
// 开启 syslogroot@SRX# set system syslog host <IP address of the remote Syslog server (i.e., Firewall Analyzer)> any anyset system syslog host 10.3.3.103 source-address 10.3.1.254// 策略开启日志root@SRX# set security policies from-zone trust to-zone untrust policy permit-all then log session-close* High-End 设备:set security log mode streamset security log source-address 10.3.1.254set security log stream trafficlogs host 10.3.1.200// 开启 policy 的日志记录 then log session-closeset security policies from-zone trust to-zone untrust policy permit-all then log session-close### 10. JSRP 维护命令 -
(1) 手工切换 JSRP Master,RG1 原 backup 将成为 Master,RG0 同样
root@SRX>
request chassis cluster failover redundancy-group 1 node 1
request chassis cluster failover redundancy-group 0 node 1
- (2) 手工恢复 JSRP 状态,按照优先级重新确定主备关系(高值优先)
root@SRX>
request chassis cluster failover reset redundancy-group 1
request chassis cluster failover reset redundancy-group 0
- (3) 查看 cluster interface
root@SRX> show chassis cluster interfaces
- (4) 查看 cluster 状态、节点状态、主备关系
root@SRX> show chassis cluster status
- (5) 禁用群集,取消 cluster 配置
root@SRX# set chassis cluster disable reboot
- (6) 恢复处于 disabled 状态的 node
当 control port 或 fabric link 出现故障时,为避免出现双 master (split-brain) 现象,JSRP 会把出现 故障前状态为 secdonary 的 node 设为 disabled 状态,即除了 RE,其余部件都不工作。想要恢复必须 reboot 该 node。
- (7) 查看群集的相关命令
root@SRX>
show chassis cluster status
show chassis cluster interfaces
show chassis cluster statistics
show chassis cluster control-plane statistics
show chassis cluster data-plane statistics
show chassis cluster status redundancy-group 0
show chassis cluster status redundancy-group 1
12. Cluster 升级 In-Service Software Upgrade (ISSU)
[SRX] ISSU/ICU upgrade limitations on SRX firewalls kb.juniper.net/InfoCenter/…
Upgrading a SRX Chassis Cluster blog.marquis.co/upgrading-a…
branch SRX devices: In-Band Cluster Upgrade (ICU)
request system software in-service-upgrade /path/to/package no-sync{primary:node0}root@SRX240-1> request system software in-service-upgrade /var/tmp/junos-srxsme-12.3X48-D50.6-domestic.tgz no-sync
high-end SRX devices: In-Service Software Upgrade (ISSU)
request system software in-service-upgrade /path/to/package reboot{primary:node0}root@SRX3400-1> request system software in-service-upgrade /var/tmp/junos-srx1k3k-12.3X48-D50.6-domestic.tgz reboot
Important note Unlike with the ICU upgrade process, you have to enter the option reboot to confirm that you want a reboot after. If you don’t use the option reboot, the command will fail. This only applies to the High End SRX devices, SRX1400, SRX3400, SRX3600, SRX5600 and SRX5800.
SRX 240b(240h) 支持不了新版本,仅仅支持到 12.1x46,并已停产 ERROR: Unsupported platform srx240b for 12.1X47 and higher
在老旧版本中,已经不适用,升级过程会中断业务。升级步骤如下:
- 升级 node 0,注意不要重启系统* 升级 node 1,注意不要重启系统.* 同时重启两个系统相关产品下载
Juniper vSRX 20.3R1 - 虚拟防火墙,云安全保护
零基础入门
对于从来没有接触过网络安全的同学,我们帮你准备了详细的学习成长路线图。可以说是最科学最系统的学习路线,大家跟着这个大的方向学习准没问题。
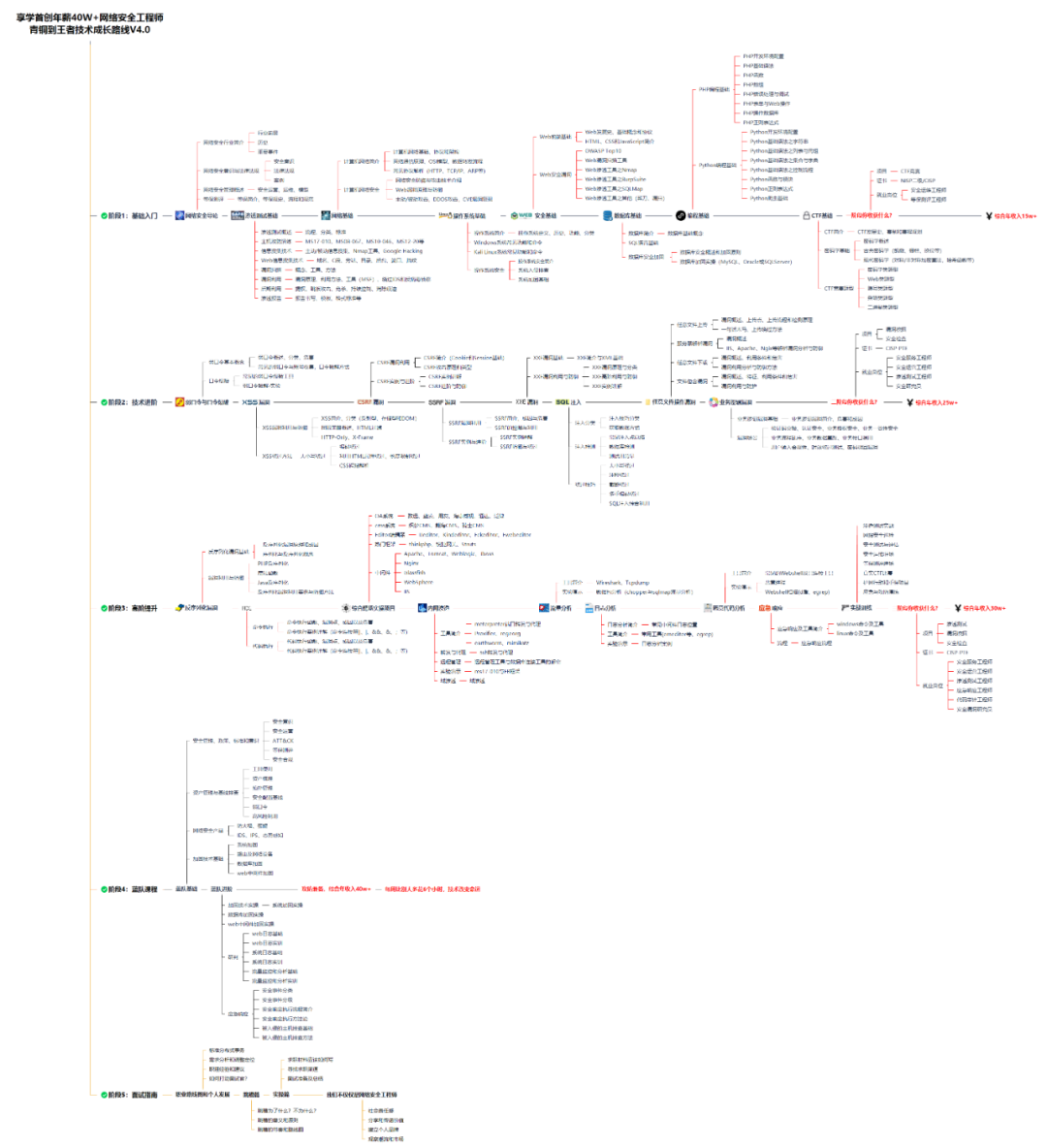
同时每个成长路线对应的板块都有配套的视频提供:

因篇幅有限,仅展示部分资料,需要点击下方链接即可前往获取
CSDN大礼包:《黑客&网络安全入门&进阶学习资源包》免费分享
视频配套资料&国内外网安书籍、文档&工具
当然除了有配套的视频,同时也为大家整理了各种文档和书籍资料&工具,并且已经帮大家分好类了。
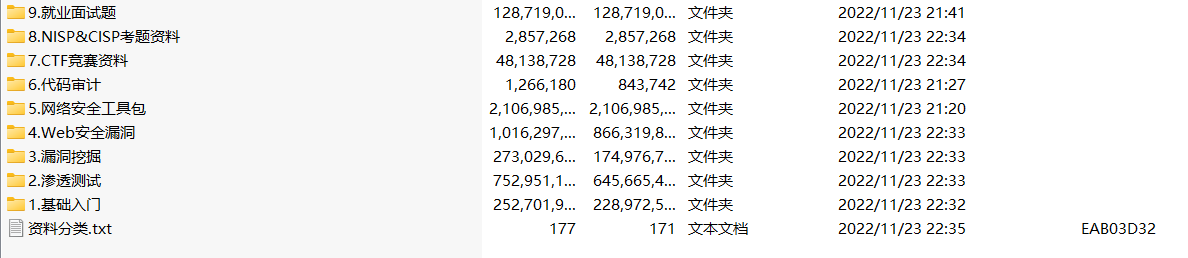
因篇幅有限,仅展示部分资料,需要点击下方链接即可前往获取
CSDN大礼包:《黑客&网络安全入门&进阶学习资源包》免费分享