介绍
OverTheWire Bandit 是一个针对初学者设计的网络安全挑战平台,旨在帮助用户掌握基本的命令行操作和网络安全技能。Bandit 游戏包含一系列的关卡,每个关卡都需要解决特定的任务来获取进入下一关的凭证。通过逐步挑战更复杂的问题,用户可以逐步提升其 Linux 系统操作和安全技能。
一、平台概述
OverTheWire 是一个提供各种网络安全游戏的平台,Bandit 是其最受欢迎的系列之一。Bandit 主要关注 Linux 系统基础知识,通过一系列逐步递进的任务,引导用户学习基本的命令行操作、文件管理、权限控制、脚本编写等技能。
二、如何参与 Bandit 挑战
- 注册和登录:无需注册,直接通过 SSH 连接到指定的服务器即可开始挑战。
- 连接服务器:每一关的连接方式和凭证会在上一关完成时提供,通常通过 SSH 连接。
- 解决任务:每一关都有特定的任务,用户需要通过执行正确的命令来解决问题并获取下一关的凭证。
- 获取下一关凭证:成功完成任务后,会得到进入下一关的密码,通过该密码登录下一关的服务器。
三、总结
OverTheWire Bandit 是一个极佳的学习和实践 Linux 基础知识的平台,逐步引导用户从简单的命令行操作到更复杂的文件和权限管理。通过完成 Bandit 的挑战,用户不仅能够提升自己的技术水平,还能够培养解决问题的思维能力。
主要技能包括:
- 基本的命令行操作(如
ls,cat,file,find等) - 文件和目录管理
- 权限控制和操作
- 处理特殊文件名和字符
- 脚本编写和自动化任务
Bandit 为学习网络安全的初学者提供了一个良好的起点,通过一步步的挑战,用户可以打下坚实的基础,为更高级的安全研究和实践做好准备。
一、Bandit Level 13
用上一关的密码登录成功
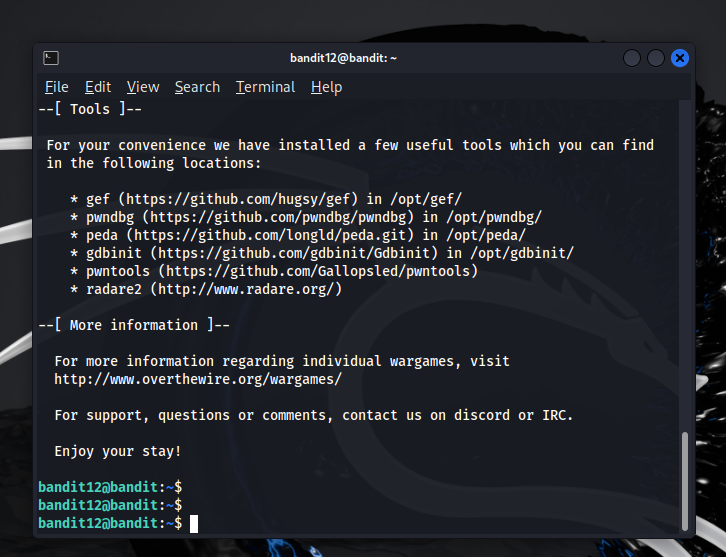

根据提示执行命令
bandit12@bandit:~$ ls
data.txt
bandit12@bandit:~$ cp data.txt /tmp/bandit12
bandit12@bandit:~$ cd /tmp/bandit12
bandit12@bandit:/tmp/bandit12$ ls
data.txt
bandit12@bandit:/tmp/bandit12$ head data.txt
00000000: 1f8b 0808 dcaa 7366 0203 6461 7461 322e ......sf..data2.
00000010: 6269 6e00 0141 02be fd42 5a68 3931 4159 bin..A...BZh91AY
00000020: 2653 5946 b21b 1500 001c 7fff dcff d2ff &SYF............
00000030: f96f b6bf 0fd6 d7ff b7bf bffd a5fe 3fef .o............?.
00000040: b6de 9fff bebe ffbc cfef f7ff b001 3b16 ..............;.
00000050: 51d0 0191 a1a0 68c9 a000 000d 321a 0680 Q.....h.....2...
00000060: 0d00 000d 000c 4c4c 101a 0006 8006 8000 ......LL........
00000070: 6834 1ea1 a699 3d4f 46a7 a880 0000 0034 h4....=OF......4
00000080: 0000 681a 1a32 34da 80d0 1a68 c803 4003 ..h..24....h..@.
00000090: 4193 2794 d1a3 4f41 1ea0 1a6d 41ea 0000 A.'...OA...mA...'
bandit12@bandit:/tmp/bandit12$ file data.txt
data.txt: ASCII text
bandit12@bandit:/tmp/bandit12$ mv data.txt data
bandit12@bandit:/tmp/bandit12$ xxd -r data > binary
bandit12@bandit:/tmp/bandit12$ ls
binary data
bandit12@bandit:/tmp/bandit12$ file binary
binary: gzip compressed data, was "data2.bin", last modified: Thu Jun 20 04:06:52 2024, max compression, from Unix, original size modulo 2^32 577
bandit12@bandit:/tmp/bandit12$ mv binary binary.gz
bandit12@bandit:/tmp/bandit12$ gunzip binary.gz
bandit12@bandit:/tmp/bandit12$ file binary
binary: bzip2 compressed data, block size = 900k
bandit12@bandit:/tmp/bandit12$ bunzip2 binary
bandit12@bandit:/tmp/bandit12$ ls
binary.out data
bandit12@bandit:/tmp/bandit12$ file binary.out
binary.out: gzip compressed data, was "data4.bin", last modified: Thu Jun 20 04:06:52 2024, max compression, from Unix, original size modulo 2^32 20480
bandit12@bandit:/tmp/bandit12$ mv binary.out binary.gz
bandit12@bandit:/tmp/bandit12$ gunzip binary.gz
bandit12@bandit:/tmp/bandit12$ ls
binary data
bandit12@bandit:/tmp/bandit12$ file binary
binary: POSIX tar archive (GNU)
bandit12@bandit:/tmp/bandit12$ ls
binary data
bandit12@bandit:/tmp/bandit12$ tar -xf binary
bandit12@bandit:/tmp/bandit12$ ls
binary data data5.bin
bandit12@bandit:/tmp/bandit12$ file data5.bin
data5.bin: POSIX tar archive (GNU)
bandit12@bandit:/tmp/bandit12$ tar -xf data5.bin
bandit12@bandit:/tmp/bandit12$ ls
binary data data5.bin data6.bin
bandit12@bandit:/tmp/bandit12$ file data6.bin
data6.bin: bzip2 compressed data, block size = 900k
bandit12@bandit:/tmp/bandit12$ bunzip2 data6.bin
bunzip2: Can't guess original name for data6.bin -- using data6.bin.out'
bandit12@bandit:/tmp/bandit12$ ls
binary data data5.bin data6.bin.out
bandit12@bandit:/tmp/bandit12$ file data6.bin.out
data6.bin.out: POSIX tar archive (GNU)
bandit12@bandit:/tmp/bandit12$ tar -xf data6.bin.out
bandit12@bandit:/tmp/bandit12$ ls
binary data data5.bin data6.bin.out data8.bin
bandit12@bandit:/tmp/bandit12$ file data8.bin
data8.bin: gzip compressed data, was "data9.bin", last modified: Thu Jun 20 04:06:52 2024, max compression, from Unix, original size modulo 2^32 49
bandit12@bandit:/tmp/bandit12$ mv data8.bin data8.gz
bandit12@bandit:/tmp/bandit12$ gunzip data8.gz
bandit12@bandit:/tmp/bandit12$ ls
binary data data5.bin data6.bin.out data8
bandit12@bandit:/tmp/bandit12$ cat data8
The password is FO5dwFsc0cbaIiH0h8J2eUks2vdTDwAn
bandit12@bandit:/tmp/bandit12$
拿到密码
FO5dwFsc0cbaIiH0h8J2eUks2vdTDwAn二、Bandit Level 14
使用上一关的密码登录成功
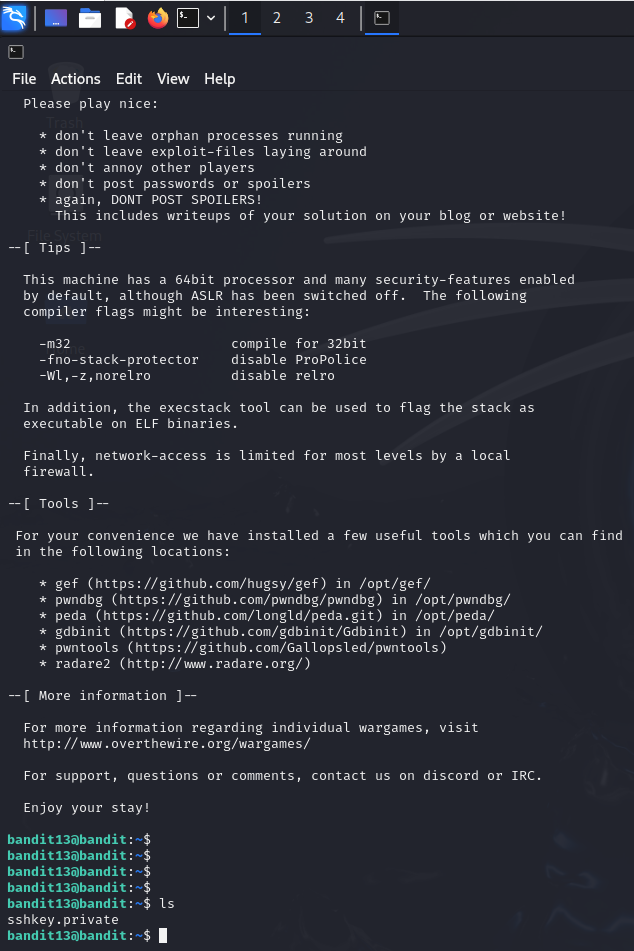

给出了密钥,直接用密钥连接即可

拿到密码
MU4VWeTyJk8ROof1qqmcBPaLh7lDCPvS三、Bandit Level 15
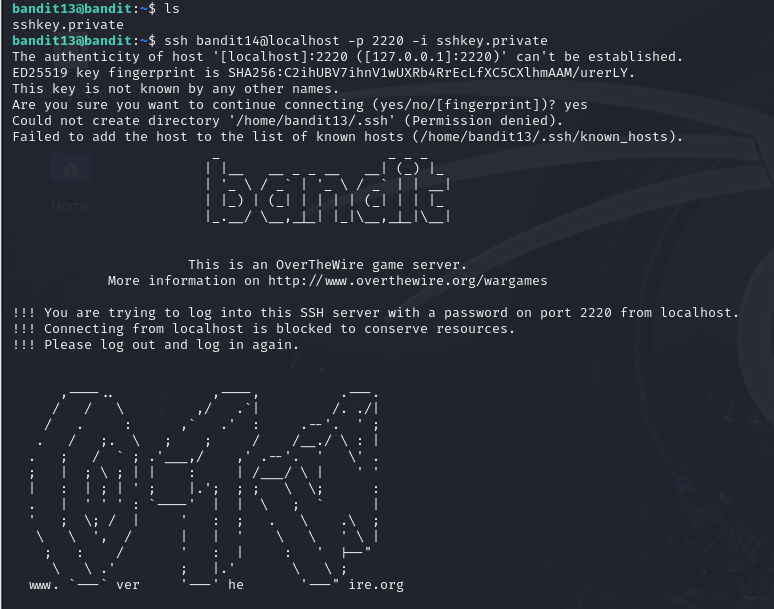
接上一关继续
使用 nc 命令
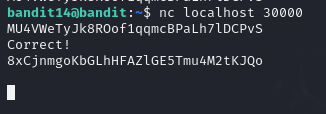
拿到密码
8xCjnmgoKbGLhHFAZlGE5Tmu4M2tKJQo四、Bandit Level 16

从这开始就上强度了
bandit14@bandit:~$ openssl s_client -connect localhost:30001
CONNECTED(00000003)
Can't use SSL_get_servername'
depth=0 CN = SnakeOil
verify error:num=18:self-signed certificate
verify return:1
depth=0 CN = SnakeOil
verify return:1
---
Certificate chain0 s:CN = SnakeOili:CN = SnakeOila:PKEY: rsaEncryption, 4096 (bit); sigalg: RSA-SHA256v:NotBefore: Jun 10 03:59:50 2024 GMT; NotAfter: Jun 8 03:59:50 2034 GMT
---
Server certificate
-----BEGIN CERTIFICATE-----
MIIFBzCCAu+gAwIBAgIUBLz7DBxA0IfojaL/WaJzE6Sbz7cwDQYJKoZIhvcNAQEL
BQAwEzERMA8GA1UEAwwIU25ha2VPaWwwHhcNMjQwNjEwMDM1OTUwWhcNMzQwNjA4
MDM1OTUwWjATMREwDwYDVQQDDAhTbmFrZU9pbDCCAiIwDQYJKoZIhvcNAQEBBQAD
ggIPADCCAgoCggIBANI+P5QXm9Bj21FIPsQqbqZRb5XmSZZJYaam7EIJ16Fxedf+
jXAv4d/FVqiEM4BuSNsNMeBMx2Gq0lAfN33h+RMTjRoMb8yBsZsC063MLfXCk4p+
09gtGP7BS6Iy5XdmfY/fPHvA3JDEScdlDDmd6Lsbdwhv93Q8M6POVO9sv4HuS4t/
jEjr+NhE+Bjr/wDbyg7GL71BP1WPZpQnRE4OzoSrt5+bZVLvODWUFwinB0fLaGRk
GmI0r5EUOUd7HpYyoIQbiNlePGfPpHRKnmdXTTEZEoxeWWAaM1VhPGqfrB/Pnca+
vAJX7iBOb3kHinmfVOScsG/YAUR94wSELeY+UlEWJaELVUntrJ5HeRDiTChiVQ++
wnnjNbepaW6shopybUF3XXfhIb4NvwLWpvoKFXVtcVjlOujF0snVvpE+MRT0wacy
tHtjZs7Ao7GYxDz6H8AdBLKJW67uQon37a4MI260ADFMS+2vEAbNSFP+f6ii5mrB
18cY64ZaF6oU8bjGK7BArDx56bRc3WFyuBIGWAFHEuB948BcshXY7baf5jjzPmgz
mq1zdRthQB31MOM2ii6vuTkheAvKfFf+llH4M9SnES4NSF2hj9NnHga9V08wfhYc
x0W6qu+S8HUdVF+V23yTvUNgz4Q+UoGs4sHSDEsIBFqNvInnpUmtNgcR2L5PAgMB
AAGjUzBRMB0GA1UdDgQWBBTPo8kfze4P9EgxNuyk7+xDGFtAYzAfBgNVHSMEGDAW
gBTPo8kfze4P9EgxNuyk7+xDGFtAYzAPBgNVHRMBAf8EBTADAQH/MA0GCSqGSIb3
DQEBCwUAA4ICAQAKHomtmcGqyiLnhziLe97Mq2+Sul5QgYVwfx/KYOXxv2T8ZmcR
Ae9XFhZT4jsAOUDK1OXx9aZgDGJHJLNEVTe9zWv1ONFfNxEBxQgP7hhmDBWdtj6d
taqEW/Jp06X+08BtnYK9NZsvDg2YRcvOHConeMjwvEL7tQK0m+GVyQfLYg6jnrhx
egH+abucTKxabFcWSE+Vk0uJYMqcbXvB4WNKz9vj4V5Hn7/DN4xIjFko+nREw6Oa
/AUFjNnO/FPjap+d68H1LdzMH3PSs+yjGid+6Zx9FCnt9qZydW13Miqg3nDnODXw
+Z682mQFjVlGPCA5ZOQbyMKY4tNazG2n8qy2famQT3+jF8Lb6a4NGbnpeWnLMkIu
jWLWIkA9MlbdNXuajiPNVyYIK9gdoBzbfaKwoOfSsLxEqlf8rio1GGcEV5Hlz5S2
txwI0xdW9MWeGWoiLbZSbRJH4TIBFFtoBG0LoEJi0C+UPwS8CDngJB4TyrZqEld3
rH87W+Et1t/Nepoc/Eoaux9PFp5VPXP+qwQGmhir/hv7OsgBhrkYuhkjxZ8+1uk7
tUWC/XM0mpLoxsq6vVl3AJaJe1ivdA9xLytsuG4iv02Juc593HXYR8yOpow0Eq2T
U5EyeuFg5RXYwAPi7ykw1PW7zAPL4MlonEVz+QXOSx6eyhimp1VZC11SCg==
-----END CERTIFICATE-----
subject=CN = SnakeOil
issuer=CN = SnakeOil
---
No client certificate CA names sent
Peer signing digest: SHA256
Peer signature type: RSA-PSS
Server Temp Key: X25519, 253 bits
---
SSL handshake has read 2103 bytes and written 373 bytes
Verification error: self-signed certificate
---
New, TLSv1.3, Cipher is TLS_AES_256_GCM_SHA384
Server public key is 4096 bit
Secure Renegotiation IS NOT supported
Compression: NONE
Expansion: NONE
No ALPN negotiated
Early data was not sent
Verify return code: 18 (self-signed certificate)
---
---
Post-Handshake New Session Ticket arrived:
SSL-Session:Protocol : TLSv1.3Cipher : TLS_AES_256_GCM_SHA384Session-ID: A81F3D2E5E6B744B874508A8E48A3976F41AE7E5D25884C351E2653400201D7FSession-ID-ctx: Resumption PSK: 97F6EEE30198DB4EA5D506D0620FF1E1796AE2D758F5CC690081923ACA3156B9B70DDA142DD2209C6FD74102280421FCPSK identity: NonePSK identity hint: NoneSRP username: NoneTLS session ticket lifetime hint: 300 (seconds)TLS session ticket:0000 - 60 61 e6 2e a8 2b fb 0f-0a aa 39 05 88 21 10 3e `a...+....9..!.>0010 - 0f d0 ec db 61 ea ce 8e-df 9a c8 ab 7d bf ff ca ....a.......}...0020 - 45 6b 7a c7 79 ad 13 e4-eb 04 7f 44 1a 1c 1f 30 Ekz.y......D...00030 - 3c 91 77 e9 b6 b4 41 3e-4d 8f c9 d8 a7 ce b3 3c <.w...A>M......<0040 - 49 12 d2 d8 0c 40 1d 0a-57 e5 22 91 26 be 69 8b I....@..W."".&.i.0050 - b2 21 60 9f 8b ae 3b ff-bf 7f 11 18 c0 44 9d 01 .!`...;......D..0060 - f9 da 3a 66 3c 57 b2 f9-62 75 07 6e fe 64 12 ba ..:f<W..bu.n.d..0070 - 98 65 60 f3 74 b2 1d 67-c4 11 27 a9 79 2f 88 18 .e`.t..g..''.y/..0080 - 08 e8 95 a3 e9 f8 0f cc-08 95 56 c4 30 e8 3c 14 ..........V.0.<.0090 - f4 7d f1 ab dd 4e b7 80-74 c7 58 a2 22 9c 15 be .}...N..t.X.""...00a0 - 4f db 42 d5 a1 b6 f9 9a-1f bd 1c 0c ac 5c 9e bd O.B..........\..00b0 - 68 33 a1 f0 36 40 06 a7-1d 74 6f 78 8d ea 62 78 h3..6@...tox..bx00c0 - b5 50 5b 16 70 32 c7 87-c9 48 37 f8 2e 38 b2 aa .P[.p2...H7..8..00d0 - b5 eb b3 fa cb 19 cb ce-12 8d 0b 5c a6 19 2d 9b ...........\..-.Start Time: 1719400555Timeout : 7200 (sec)Verify return code: 18 (self-signed certificate)Extended master secret: noMax Early Data: 0
---
read R BLOCK
---
Post-Handshake New Session Ticket arrived:
SSL-Session:Protocol : TLSv1.3Cipher : TLS_AES_256_GCM_SHA384Session-ID: B84C720BEA6C81F27BDA69DDC5C85CC06975AB01F4F496A660376224221970F4Session-ID-ctx: Resumption PSK: F13872218674CAAEA6743D06B91F550490375CAA9B8ABCF8AE2B903126CDA7554A36D3DCAAB315E5E5E153E6DFCACF6APSK identity: NonePSK identity hint: NoneSRP username: NoneTLS session ticket lifetime hint: 300 (seconds)TLS session ticket:0000 - 60 61 e6 2e a8 2b fb 0f-0a aa 39 05 88 21 10 3e `a...+....9..!.>0010 - ff 2c 52 d9 6f 37 64 1e-df 41 10 52 33 65 66 79 .,R.o7d..A.R3efy0020 - e6 bc f8 28 d9 9e dc 1a-be 50 a8 de 3c 5c 5d 8d ...(.....P..<\].0030 - 6b cc 7a eb df ac 97 e9-ad 8b ec 9f c8 67 3c 02 k.z..........g<.0040 - b4 e6 4c ae 2f 2d d8 06-33 fd 9b 71 fd 76 bb 6b ..L./-..3..q.v.k0050 - 81 2c 9f 4d 46 7e 60 d2-49 45 db c9 cd 16 44 55 .,.MF~`.IE....DU0060 - 74 6e 1d 8d 71 6b b4 08-3c 92 3a 45 76 e5 66 31 tn..qk..<.:Ev.f10070 - a6 f9 ce b7 e9 25 39 82-bc a0 3c ac 26 67 70 81 .....%9...<.&gp.0080 - 84 47 1a a9 c0 94 68 f6-40 7d 47 86 ef e2 16 79 .G....h.@}G....y0090 - 09 2f 66 57 bf 30 bb 79-31 07 22 38 75 b5 cd ef ./fW.0.y1.""8u...00a0 - 40 94 ca 81 d7 fe a7 c1-e0 f3 87 fe 2c cd 8f 36 @...........,..600b0 - a4 42 d2 59 7f e5 0f 72-ed f6 c3 3a df 15 b3 32 .B.Y...r...:...200c0 - 43 e3 b5 2c 9f 5a e9 57-db d3 0b 84 31 09 20 88 C..,.Z.W....1. .00d0 - 9e 28 11 45 a1 34 db ce-3f a0 e7 a6 cf ee f4 98 .(.E.4..?.......Start Time: 1719400555Timeout : 7200 (sec)Verify return code: 18 (self-signed certificate)Extended master secret: noMax Early Data: 0
---
read R BLOCK
8xCjnmgoKbGLhHFAZlGE5Tmu4M2tKJQo
Correct!
kSkvUpMQ7lBYyCM4GBPvCvT1BfWRy0Dxclosed
bandit14@bandit:~$拿到密码
kSkvUpMQ7lBYyCM4GBPvCvT1BfWRy0Dx五、Bandit Level 17

这里的话通过查看文件得到加密后的文件


拿到密码
kSkvUpMQ7lBYyCM4GBPvCvT1BfWRy0Dx六、Bandit Level 18
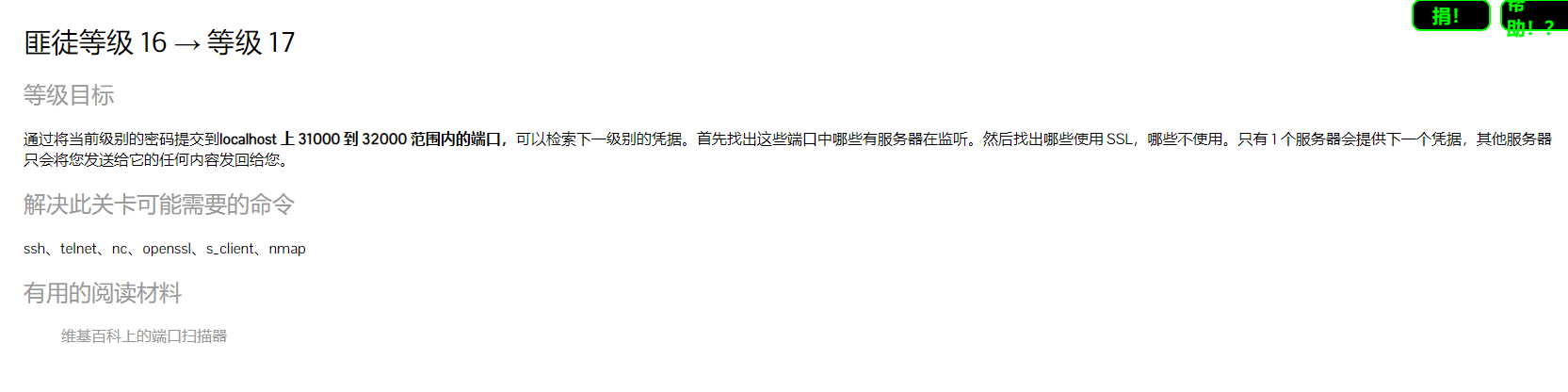
根据题目先扫描端口
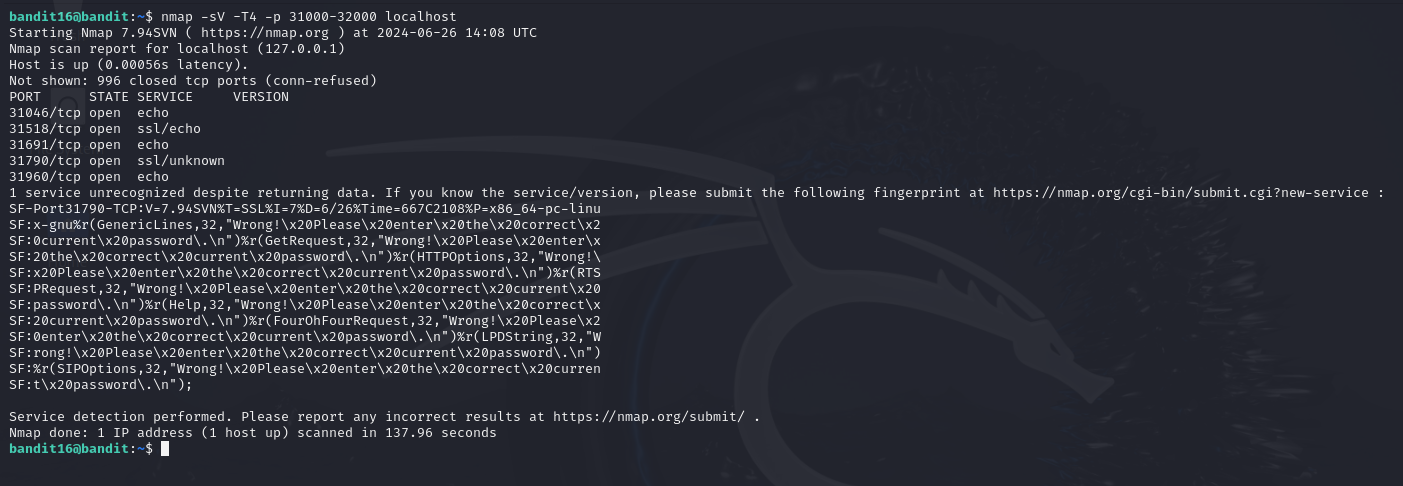
发现有两个端口是 SSL,这里剧透一下是 31790(注意:openssl 有问题)
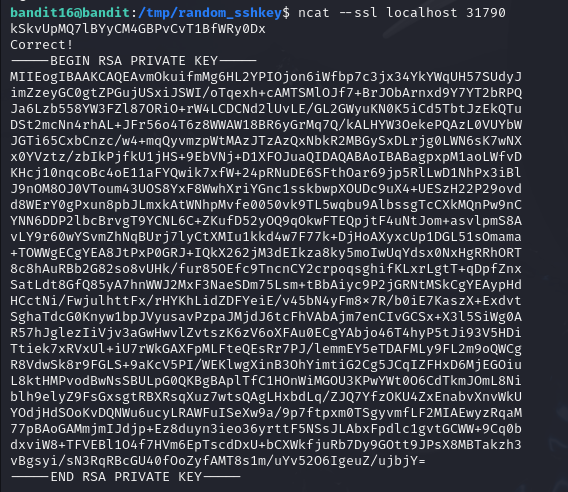
将密钥复制粘贴到一个 key 文件中,然后更改权限为 400,最后连接


七、Bandit Level 19

根据题目先查看文件

使用命令 diff 比较不同,两个文件都是 100 行,只有一行不同

拿到密码
x2gLTTjFwMOhQ8oWNbMN362QKxfRqGlO退出服务器登录

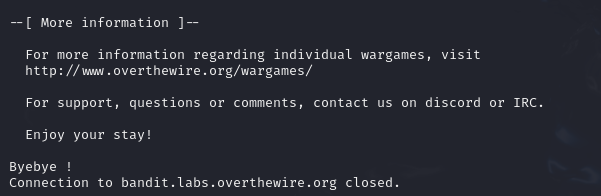
八、Bandit Level 20
看题目,难怪会直接退出
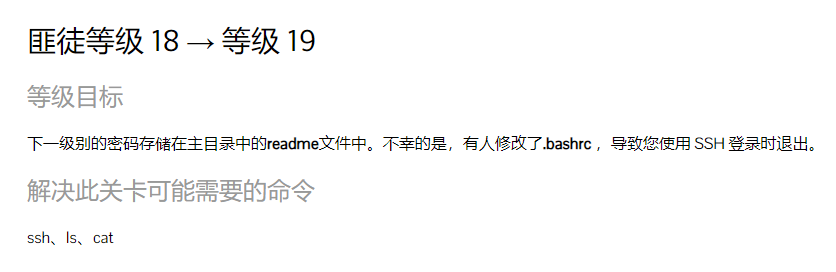
登录之前的用户查看可用的 shell

指定别的 shell 登录

拿到密码
cGWpMaKXVwDUNgPAVJbWYuGHVn9zl3j8九、Bandit Level 21
先用之前的密码登录
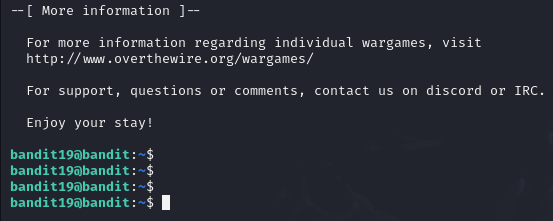

可以看到直接运行提示需跟上参数 id,跟上执行后被分配了 bandit20 的 id,意味着我们可以像 bandit20 一样运行命令
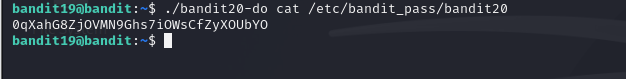
拿到密码
0qXahG8ZjOVMN9Ghs7iOWsCfZyXOUbYO十、Bandit Level 22
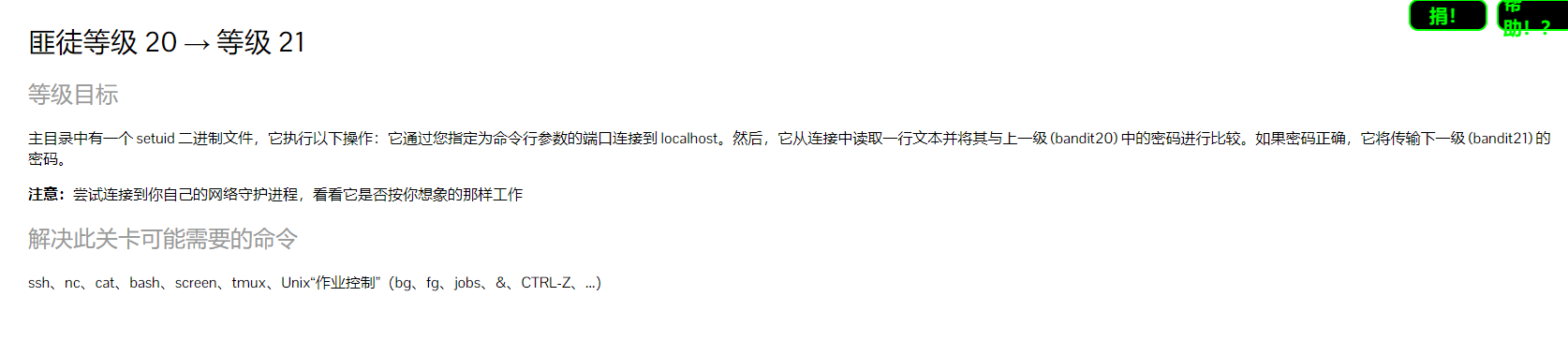
先通过上一关密码连接
我们需要做的第一件事是在系统上的任何端口上设置一个监听器,如果我们使用二进制文件连接到该端口,它将返回上一级密码。我们可以使用命令设置一个监听器
拿到密码
EeoULMCra2q0dSkYj561DX7s1CpBuOBt十一、Bandit Level 23
先使用上一关密码登录


让我们看看系统上所有的 cron 作业
![]()
先看用户 bandit22 的

发现有一个执行的脚本,看看内容
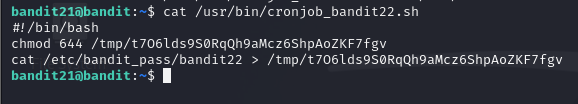
第一条是改权限,第二条是将密码写入另一个文件中,查看密码
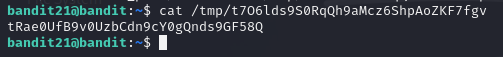
查看密码
tRae0UfB9v0UzbCdn9cY0gQnds9GF58Q十二、Bandit Level 24
使用上一关的密码登录

命令与上一关一样

查看下脚本
#!/bin/bashmyname=$(whoami)
mytarget=$(echo I am user $myname | md5sum | cut -d ' ' -f 1)echo "Copying passwordfile /etc/bandit_pass/$myname to /tmp/$mytarget"cat /etc/bandit_pass/$myname > /tmp/$mytarget
执行命令搞出 mytarget 值
这个值就是目录,所以直接查看即可
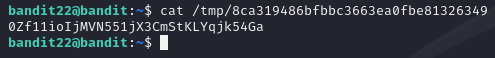
拿到密码
0Zf11ioIjMVN551jX3CmStKLYqjk54Ga

![[hive] posexplode生成从去年一月一号,到本月的月时间表](https://img-blog.csdnimg.cn/direct/5decb5e637024900a5ea082da2940a3d.png)
