公钥或非对称密码学的发展是整个密码学历史上最伟大的,也许是唯一真正的革命。The development of public-key, or asymmetric, cryptography is the greatest and perhaps the only true revolution in the entire history of cryptography.
公钥算法基于数学函数,而不是替换和排列。public-key algorithms are based on mathematical functions rather than on substitution and permutation.
公钥加密是不对称的,涉及使用两个单独的密钥,两个密钥的使用在机密性、密钥分发和身份验证方面具有深远的影响。public-key cryptography is asymmetric, involving the use of two separate keys, the use of two keys has profound consequences in the areas of confidentiality, key distribution, and authentication.
几个常见的误解Several Common Misconceptions
公钥加密更安全?Public-key encryption is more secure?
事实上,任何加密方案的安全性都取决于密钥的长度和破解密码所涉及的计算工作量。In fact, the security of any encryption scheme depends on the length of the key and the computational work involved in breaking a cipher.
原则上,从抵抗密码分析的角度来看,对称加密或公钥加密都没有什么优势。There is nothing in principle about either symmetric or public-key encryption that makes one superior to another from the point of view of resisting cryptanalysis.
公钥加密使对称加密过时了?Public-key encryption is a general-purpose technique that has made symmetric encryption obsolete?
相反,由于当前公钥加密方案的计算开销,似乎没有可以预见的放弃对称加密的可能性。On the contrary, because of the computational overhead of current public-key encryption schemes, there seems no foreseeable likelihood that symmetric encryption will be abandoned.
公钥加密对密钥管理和签名应用程序的限制几乎是普遍接受的。The restriction of public-key cryptography to key management and signature applications is almost universally accepted.
与对称加密的密钥分发中心所涉及的相当麻烦的握手相比,使用公钥加密时密钥分发是微不足道的吗?Key distribution is trivial when using public-key encryption, compared to the rather cumbersome handshaking involved with key distribution centers for symmetric encryption?
需要某种形式的协议,通常涉及一个中央代理,所涉及的过程并不比对称加密所需的过程更简单,也不更有效。Some form of protocol is needed, generally involving a central agent, and the procedures involved are not simpler nor any more efficient than those required for symmetric encryption.
Applications
Encryption/decryption: The sender encrypts a message with the recipient’s public key, and the recipient decrypts the message with the recipient’s private key.
Digital signature: The sender “signs” a message with its private key.
Key exchange: Two sides cooperate to exchange a session key, which is a secret key for symmetric encryption generated for use for a particular transaction (or session) and valid for a short period of time.
Requirements
It is computationally easy to generate a key pair.
It is computationally easy for a sender, knowing the public key and the message to be encrypted, to generate the corresponding ciphertext.
It is computationally easy for the receiver to decrypt the ciphertext using the private key.
It is computationally infeasible for an adversary, knowing the public key, to determine the private key.
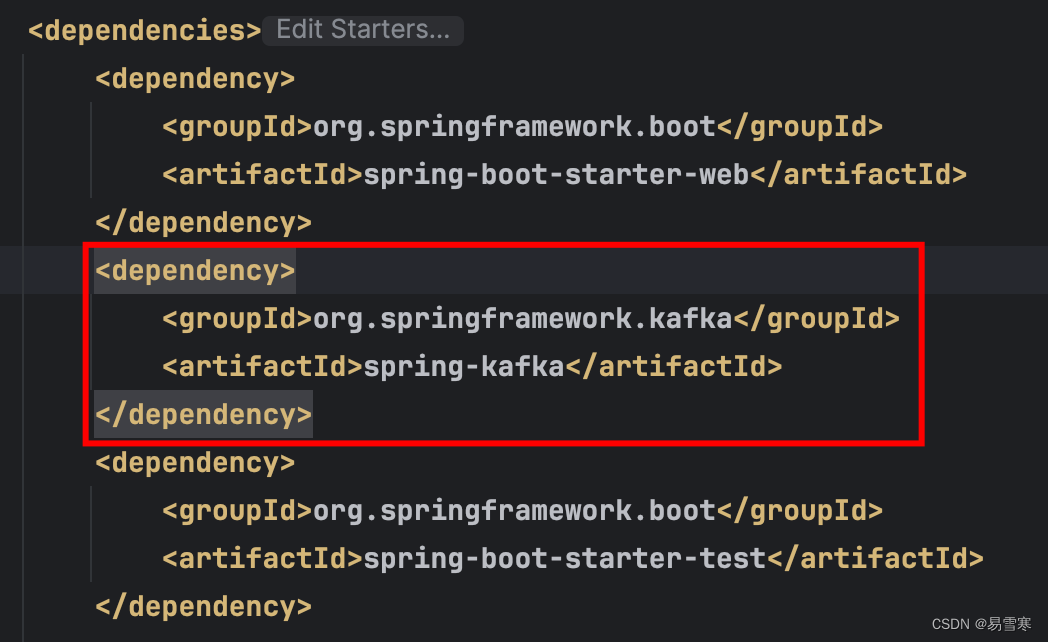
RSA
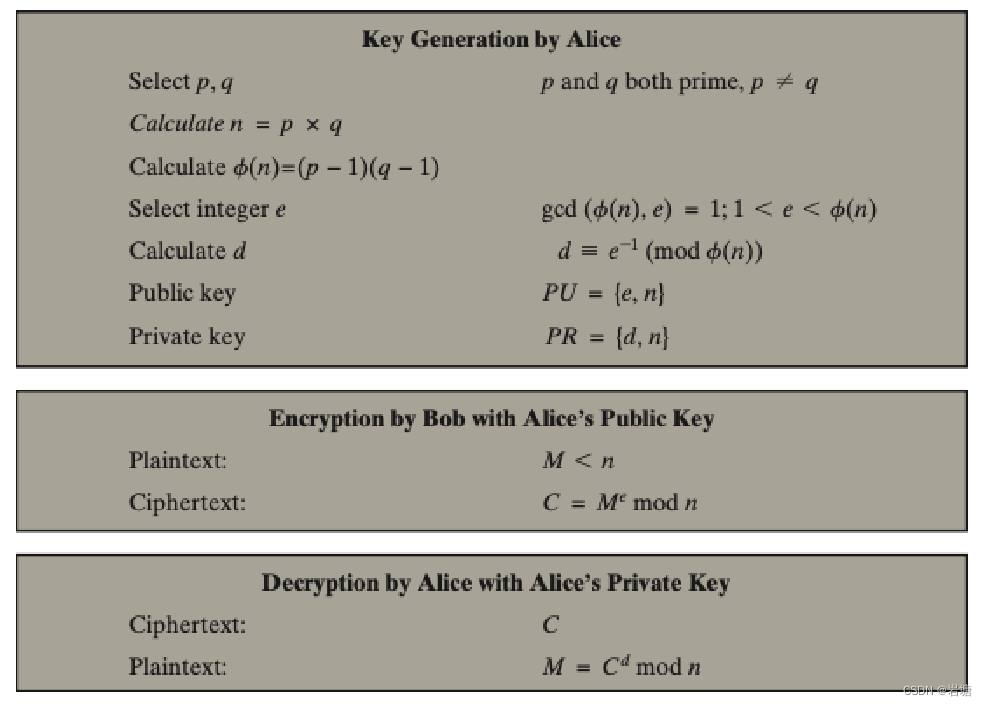
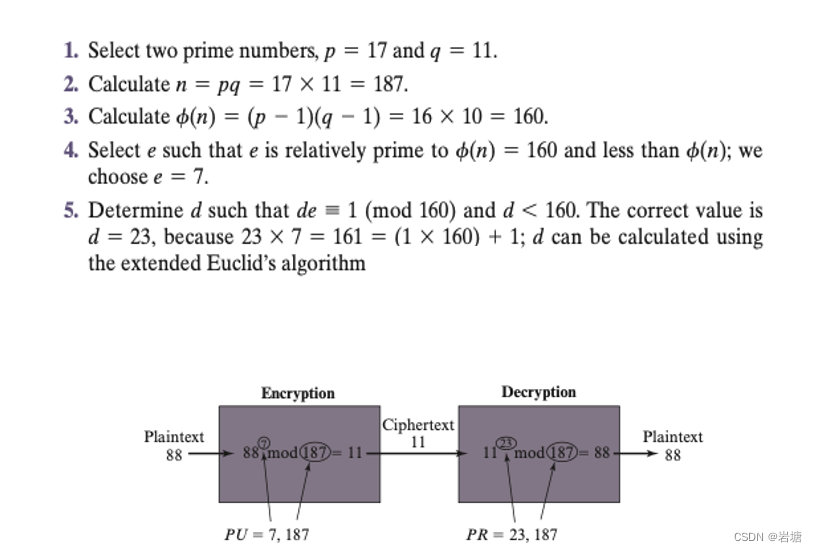
The correctness of encryption an decryption?
How to calculate d?
How to generate big prime?
Millar-Rabin algorithm
The calculation of encryption and decryption.
为什么安全?
-
大数分解问题:RSA的安全性基于大整数分解的困难程度。在RSA中,安全性依赖于两个非常大的质数的乘积。目前,尚未发现一种有效的算法能够在合理的时间内将一个大合数分解成其质因数。即使目前已知的最优算法(如大整数分解算法)也需要花费非常大的计算资源来破解较大的 RSA 密钥。因此,目前的计算资源尚不足以威胁 RSA 加密的安全性。
-
离散对数问题:RSA的安全性也依赖于离散对数问题的困难程度。在有限域上的离散对数问题是一个基本的数学难题,即给定一个底数、一个模数和一个指数,求解指数的问题。在RSA中,对一个大整数取模的指数运算在数学上等价于求解离散对数问题。目前尚未找到一种有效的算法能够在合理的时间内解决离散对数问题,尤其是在大整数域上。
哈希函数加密Hash Functions
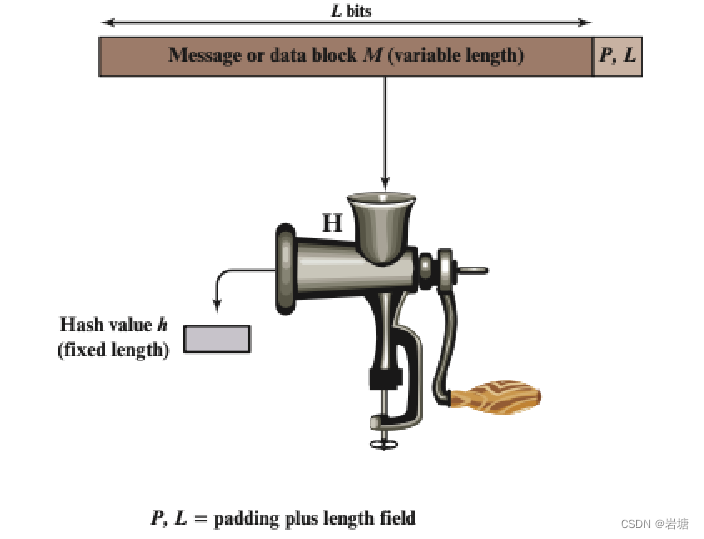
A hash function H accepts a variable-length block of data M as input and produces a fixed-size result h = H(M), referred to as a hash value or a hash code. The kind of hash function needed for security applications is referred to as a cryptographic hash function.
A cryptographic hash function is an algorithm for which it is computationally infeasible (because no attack is significantly more efficient than brute force) to find either
a data object that maps to a pre-specified hash result(the one-way property)
two data objects that map to the same hash result(the collision-free property)
Secure Hash Algorithm (SHA)
哈希加密的应用Applications of Hash Functions
信息认证Message Authentication
消息身份验证是用于验证消息完整性的机制或服务。Message authentication is a mechanism or service used to verify the integrity of a message.
数据完整性:接收到的数据与发送的完全相同(即,没有修改、插入、删除或重放)。that data received are exactly as sent (i.e., there is no modification, insertion, deletion, or replay).
数据有效:在许多情况下,需要身份验证机制确保所声称的发送方身份是有效的。In many cases, there is a requirement that the authentication mechanism assures that the purported identity of the sender is valid.
当使用散列函数提供消息身份验证时,散列函数值通常被称为消息摘要。When a hash function is used to provide message authentication, the hash function value is often referred to as a message digest.